10 Most Secure Linux Distros For Complete Privacy & Anonymity | 2017 Edition

Short Bytes: One of the most compelling reasons to use Linux is its ability to deliver a secure computing experience. There are some specialized secure Linux distros for security that add extra layers and make sure that you complete your work anonymously and privately. Some of the popular secure Linux distros for 2017 are Tails, Whoix, Kodachi, etc.
Why should I use a privacy-focused Linux distribution?
While Linux and macOS are considered more secure as compared to Windows operating system, there are some specialized Linux distros that cater to the needs of security enthusiasts. By using technologies like TOR, sandboxing, firewalls, etc., anonymous Linux distros deliver extra layers of security.
However, due to tons of choices available in the open source world of Linux, often, inexperienced users get confused and choose the wrong operating system. To fulfill that needs, we keep publishing different lists of best Linux distros from time to time. Before going ahead and taking a look at the most secure Linux distros, don’t forget to check out our other popular articles:
- Best Linux Distros for kids
- Linux Distro For Beginners
- Most Beautiful Linux Distros
- Best Linux Distro For Gamers
- Best Lightweight Linux Distros
- Overall Best Linux Distributions
- Best Linux Distros For Programming
- Best Operating Systems For Hacking
10 Best And Most Secure Linux Distributions
1. Tails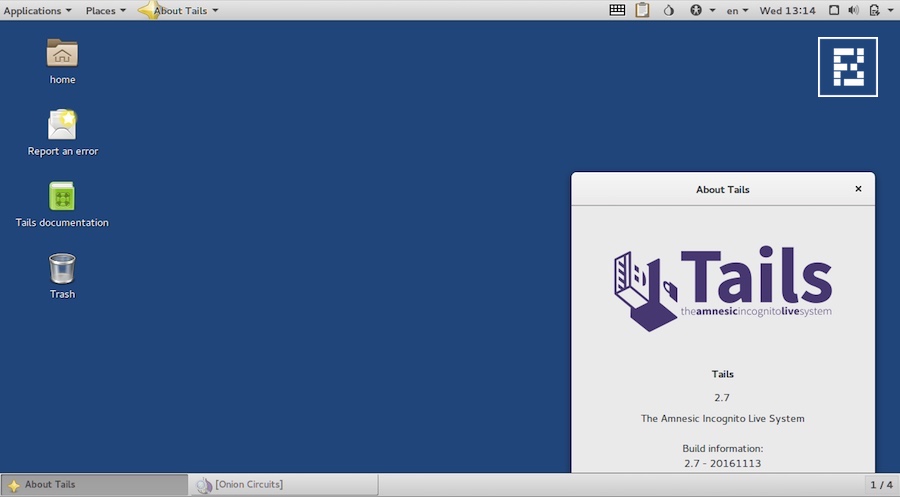
For many of us, Tails is the default choice while looking for a Linux for security solution. Tails, or The Amnesic Incognito Live System, is a Debian-based Linux distribution that’s one of the most secure operating systems you’ll ever get. Tails, an open source distribution, was first released about 8 years ago. With the help of redirecting all the web traffic through Tor, Tails achieves privacy through anonymity.
As Tails stores everything in RAM and avoids the usage of the hard disk, it erases everything once it’s shut down. Moreover, Tails is also suitable for general usage, thanks to the default GNOME desktop environment.
2. Whonix
Just like Tails, Whonix secure Linux distro is also based on Debian GNU/Linux. This private operating system consists of two virtual machines. While one VM is a “Tor Gateway” running Debian, other one is a “Workstation.” Please note that Whonix is installed on a user-provided host OS that could be Linux, Windows, macOS, or Qubes OS. By utilizing Tor’s open and distributed relay network, Whonix defeats the network surveillance possibilities.
This Linux for security purposes does its best to hide the real IP address of the user. Also, many pre-installed applications are stream-isolated in Whonix and they use a dedicated Tor SocksPort for extra security.
3. Qubes OS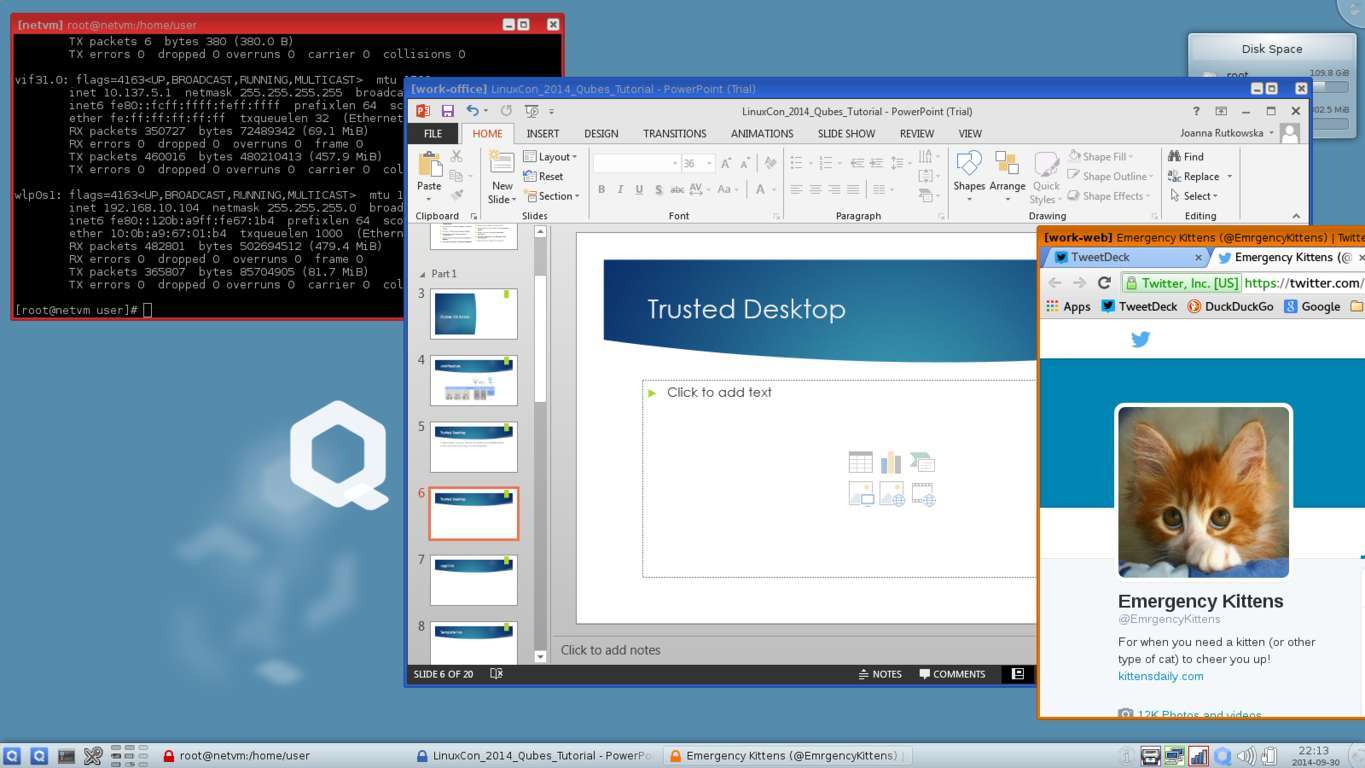
Qubes OS, which is also called the world’s most secure operating system, is a security-oriented system which performs virtualization by Xen hypervisor. For those who don’t know, a hypervisor mimics the hardware and allows running multiple virtual machines. The user environment for Qubes OS could be Fedora, Debian, Whoix, and Windows. Just like Tails Linux for security, Qubes OS too has been approved by NSA whistleblower Edward Snowden.
In Qubes, the isolation is performed by turning hardware controllers into functional domains. It also separates your digital life in different levels of trust, for e.g., work domain, shopping domain, random domain, etc. All these domains are run in different virtual machines. With this technique, one exploit doesn’t allow the attacker to take over the entire computer.
4. Subgraph OS
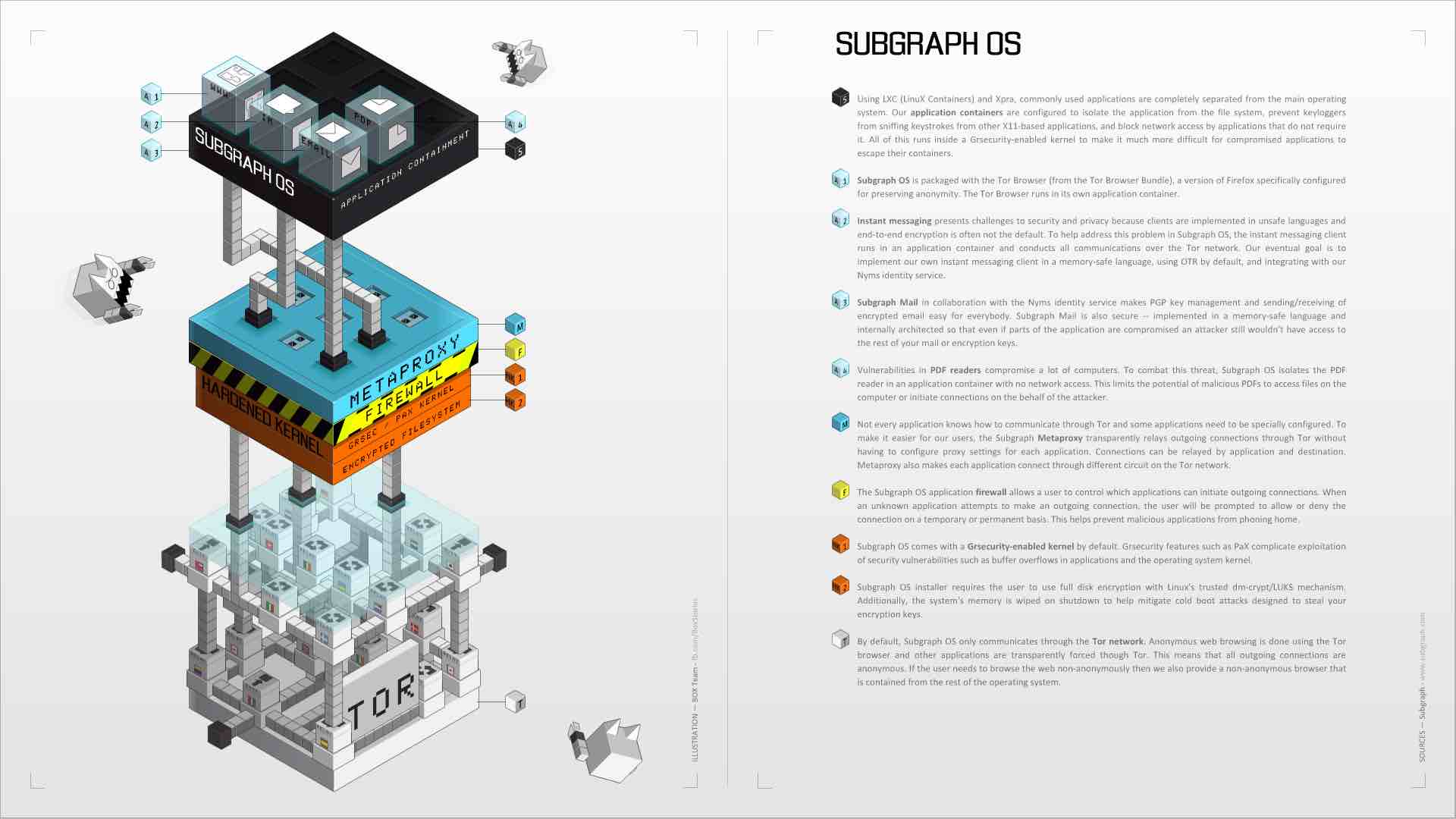
Subgraph OS is a Debian-based secure Linux distro that promises to provide anonymous digital experience and hardening features. Also approved by Edward Snowden, Subgraph OS has been designed to avert different malware attacks. Subgraph OS is still in Alpha stage but it’s capable of being a secure communication platform along with providing a familiar user interface.
As expected, Subgraph OS runs in a sandboxed environment that runs applications like web browser, email client with in-built encryption, LibreOffice, PDF viewer, video player, Hexchat, etc. It includes a hardened kernel with grsecurity/PaX patch for strong security protection to all processes. This anonymous Linux distro’s most custom code is written in Go, which is a memory safe language. It also includes an application firewall that makes sure that user is protected from unexpected outbound connections.
5. Discreete Linux
Just like many other entries on this list, Discreete Linux is a free software project that can be used by anyone who wishes to lead an anonymous digital life. Some of you might be knowing this secure Linux distro as Ubuntu Privacy Remix. Well, now it’s based on Debian and it has got a new name too. It promises to save the users against the trojan-powered surveillance attacks. It’s currently in beta stage.
Discreete Linux calls itself suitable for people who don’t have deeper knowledge of computing but they regard internet security as their primary concern. With the help of encryption and isolated environment, Discreete Linux prepares a secure work environment. The kernel modules on this anonymous Linux distro can only be installed if they are digitally signed by the developer team. Moreover, it doesn’t even support internal hard drives or network hardware. Instead, it stores all its data inside the RAM or an external thumb drive.
6. Kodachi
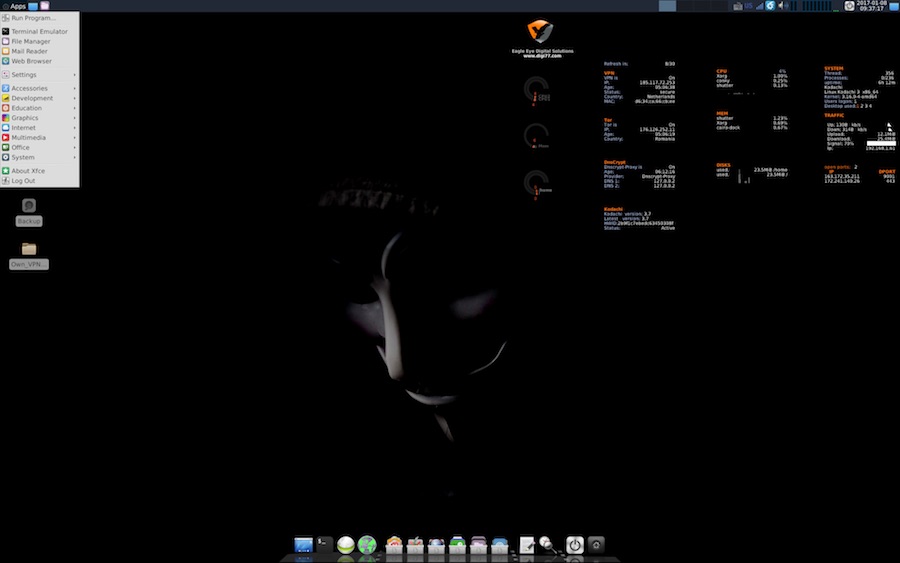
Kodachi Linux is a security-focused operating system based on Debian GNU/Linux. It aims to provide a secure computing experience. To install Kodachi and get it up and running is simple and you don’t need to invest time or effort. Kodachi Linux for security gives you the option to boot from the PC hardware or go with the external USB drive option for extra security.
By running a Kodachi system with active VPN connection, TOR, and DNScrypt service ensures a good level of privacy. All the connections to the internet are forced to pass through the previously mentioned services. The entire operating system runs from your volatile RAM memory, so after shutting down no trace of activity is left. Kodachi Linux also ships with latest privacy tools for emails, encryption, and instant messaging. The Xfce desktop environment makes it even more useful on older machines.
7. TENS
TENS Linux for security stands for Trusted End Node Security. It was previously known as LPS, or Lightweight Portable Security. Before telling you more about TENS Linux, let me mention that it’s distributed and developed by the United States Department of Defense. So, if you can make peace with that, let’s take a look at its great features.
Based on Arch Linux, TENS secure Linux OS can run on any Intel-powered machine. As it only boots in RAM, it serves as a secure end node for the users. It comes loaded with Encryption Wizard, which is a simple and strong encryption software for protection of sensitive information. TENS Linux also supports CAC and PIV access nodes that are used on American government websites. Overall, it has a minimal set of applications to ensure lesser chances of infection and better performance.
8. Tin Hat
Derived from the hardened Gentoo, Tin Hat Linux is a secure operating system that wishes to deliver a fast and secure Linux experience. For complete security, Tin Hat Linux lives entirely in RAM and doesn’t mount any file system directly from boot device, thus, avoiding any chance of leaving any data behind. As expected, you can boot it from a CD or USB flash drive.
Please note that before you start working with Tin Hat Linux for security and anonymity, you should have a knowledge of how Gentoo Linux works. You can run it both on 32-bit and 64-bit hardware architectures. The desktop environment is built around GNOME, which you’ll surely find familiar. Many applications like Firefox, email client, LibreOffice, and video player are shipped pre-installed on Tin Hat Linux.
9. IprediaOS
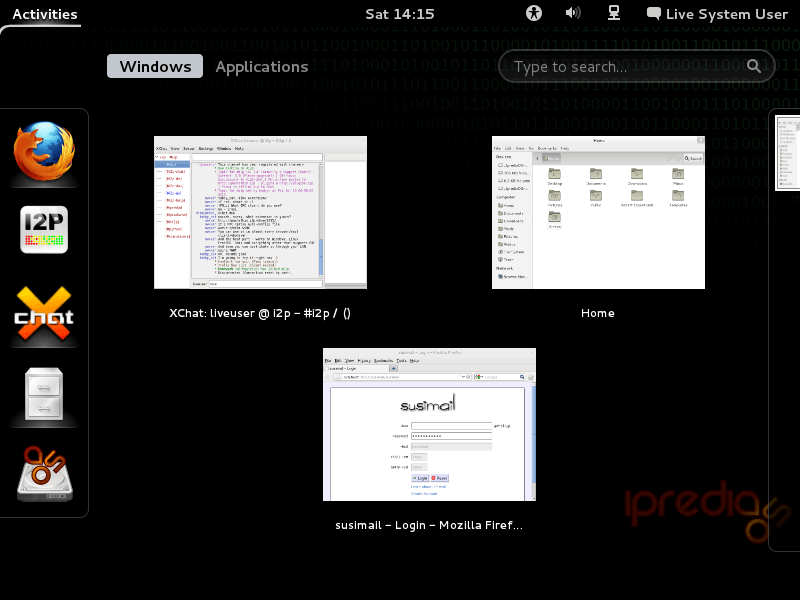 If you read our article on the best alternatives to Tor browser, you’d find I2P at the top. It’s a an anonymous P2P communication layer that’s created using open source tools. Based on the same, IprediaOS reroutes all its traffic via I2P and makes sure that all your online activity doesn’t come under radar. Wrapped in multiple layers of encryption, I2P network is dynamic and distributed, without any trusted parties. IprediaOS, a secure distro for 2017, is based on Fedora-based Linux OS. You can give it a try if you’re a Fedora loyalist.
If you read our article on the best alternatives to Tor browser, you’d find I2P at the top. It’s a an anonymous P2P communication layer that’s created using open source tools. Based on the same, IprediaOS reroutes all its traffic via I2P and makes sure that all your online activity doesn’t come under radar. Wrapped in multiple layers of encryption, I2P network is dynamic and distributed, without any trusted parties. IprediaOS, a secure distro for 2017, is based on Fedora-based Linux OS. You can give it a try if you’re a Fedora loyalist.
10. Alpine Linux
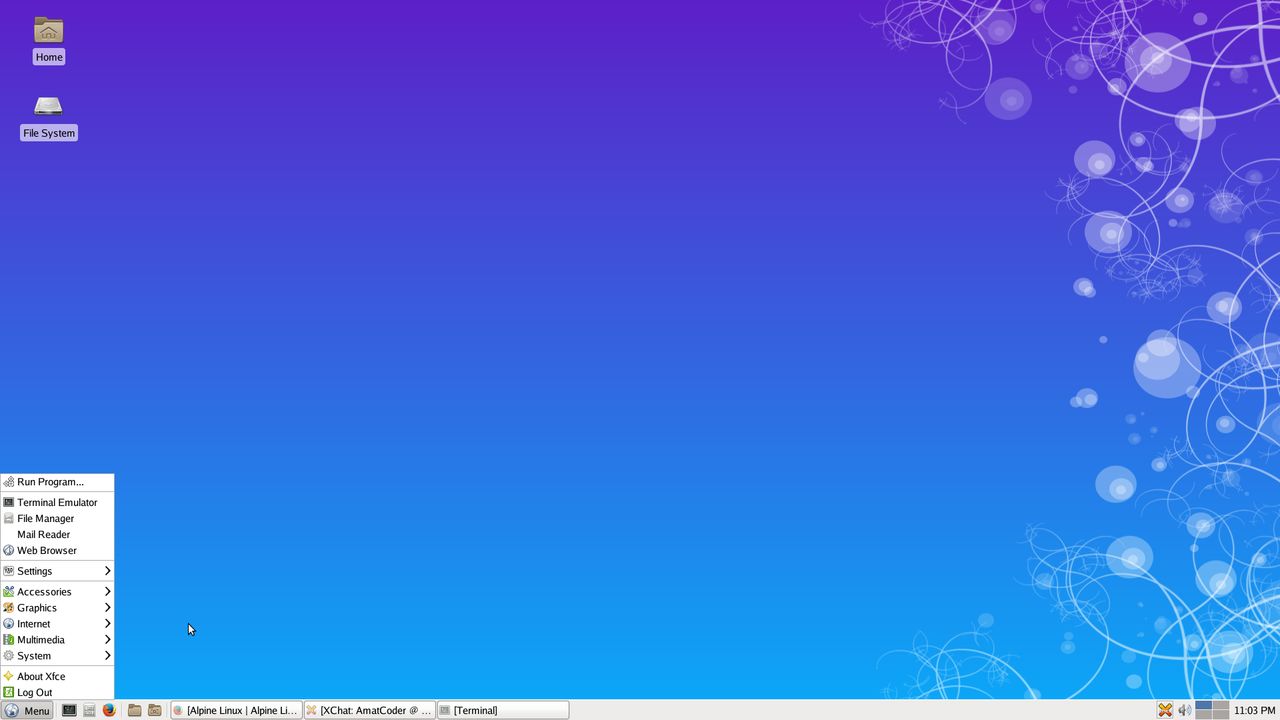 Alpine Linux has been primarily designed for the power users who value security, resource efficiency, and simplicity. This secure Linux distro was started as a fork of the LEAF project. Contrary to LEAF, which aimed to fit an OS on a floppy disk, Alpine Linux wishes to include some heavyweight packages, better security features, and newer kernel.
Alpine Linux has been primarily designed for the power users who value security, resource efficiency, and simplicity. This secure Linux distro was started as a fork of the LEAF project. Contrary to LEAF, which aimed to fit an OS on a floppy disk, Alpine Linux wishes to include some heavyweight packages, better security features, and newer kernel.
This secure Linux for privacy, uses its own package management system, apk-tools. It can be installed as a run-from-RAM OS. Built around musl libc and busybox, Alpine Linux’s kernel is patched with an unofficial port of grsecurity/Pax. Also, all userland binaries are compiled as Position Independent Executables (PIE).
Notable Mentions
Apart from the above-mentioned security focused Linux distros for 2017, there are many other options as well, and that’s the beauty of Linux. Some of the notable mentions that I’d love to elaborate in future updates of this article are listed below:
- Tor-ramdisk
- JonDo Live CD
- CoreOS
Which secure Linux distribution is your preferred choice? Tell us your views in comments below.
Also Read: Best Hacking Tools Of 2017 For Windows, Linux, And OS X