Linux Security Alert: Tons Of Linux Kernel USB Flaws Found By Google Hacker
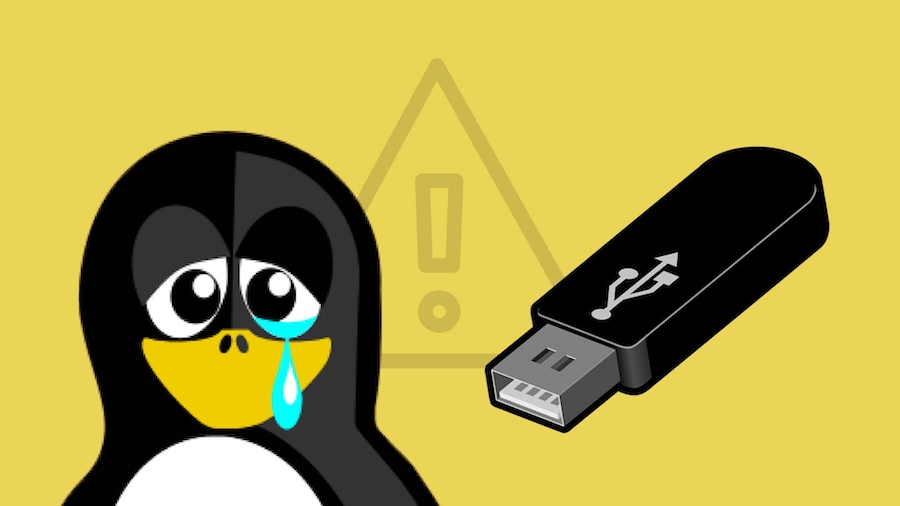
Konovalov found these 14 Linux USB flaws using Syzkaller, a kernel fuzzing tool, and reported them. “All of them can be triggered with a crafted malicious USB device in case an attacker has physical access to the machine,” according to him.
As said above, it should be pointed out that the attacker must have a physical access to the machine for carrying out the attack. But, this pre-requirement shouldn’t encourage you to downplay the gravity of the situation. In offices, flights, other public places, etc., there are numerous chances of triggering the attack.
Such flaws can also be used to hack the air-gapped systems that are not connected to the internet. In such cases, USBs are the only means of infecting a machine with exploit code.
Past studies have also shown that common public is habitual of picking up random and unattended USB drives and inserting them in their PCs without any second thought. This is another way of infecting the machine with malware to exploit a bug.
While most of the bugs can cause denial-of-service, few can be exploited to execute code in the kernel. These 14 reported bugs are actually a part of a larger list of 79 flaws (Via: Bleeping Computer) found by Konovalov. Out of these bugs, many are unreported and unpatched.
The Fossbytes readers are advised to make sure that their machines are safe when they remain attended. Also, picking up and using random USB drives is heavily discouraged.
Also Read: What is WebUSB? How It Helps Connecting USB Devices To The Web