Critical WordPress Plugin Flaw Makes 400K Sites Vulnerable To Attack

Researchers have found serious vulnerabilities in three WordPress plugins that have been installed on 400,000 websites — leaving them wide open for cyberattacks.
The bugs have been found in InfiniteWP, WP Time Capsule, and WP Database Reset plugins. These are similar types of authorization bypass bugs that allow anyone to access the backend of a website without passwords.
InfiniteWP Client
This plugin is the most severely affected by the authentication bypass vulnerability and more than 300,000 websites have InfiniteWP Client installed on them.
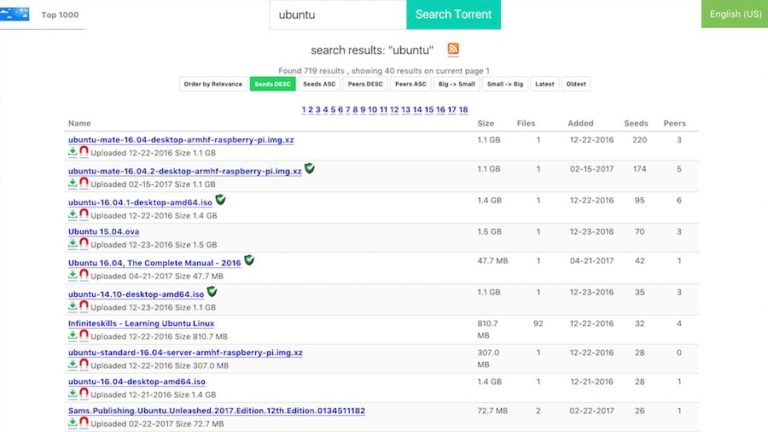
InfiniteWP Client basically allows administrators to manage multiple websites from a single server. However, by leveraging the flaw anyone can log in to an admin account without any credentials.
This would allow hackers to delete content, add new accounts, and execute a whole bunch of other malicious activities.
To exploit this vulnerability, one only requires the username of a valid account and inclusion of a malicious payload that is sent in a POST request to a vulnerable site.
This bug arises from a feature that lets users to automatically log in as an administrator without providing a password.
In case you are running InfiniteWP Client version 1.9.4.4 or lower on your website, you should update to 1.9.4.5 immediately.
WP Time Capsule
WP Time Capsule also suffers from an authentication bypass flaw that allows hackers to log in as admin. This plugin basically makes it easy to backup website data and about 20,000 websites have this plugin.
To leverage this flaw, attackers need to include a string in a POST request which helps them obtain a list of all admin accounts and automatically login to the first one.
A patch has been rolled out in version 1.21.16 so you should update your website right away if it is still running an earlier version.
WP Database Reset
The third bug was found in the WP Database Reset plugin which is installed in nearly 80,000 websites. It lets anyone reset the database to its original WordPress state within just a few clicks, thus wiping out all the data including posts, pages, users, and more.
The bug stems from reset functions that haven’t been secured by the standard capability checks or security nuances. The exploitation of this flaw can result in the complete loss of data or a site reset.
Another security flaw in WP Database Reset leads to a privilege-escalation vulnerability that lets any authenticated user (even those have restricted system rights) gain admin privileges and lock out all other users.
To avoid falling victim to such attacks, site administrators using this plugin should update to version 3.15 to patch both the bugs.
Amidst this potential threat, the only good news is that there’s no report of these vulnerabilities being exploited in the wild yet.
You can learn more about all the flaws here.