The Most Important Fight For Data Security: Why Apple Must Win Against FBI?
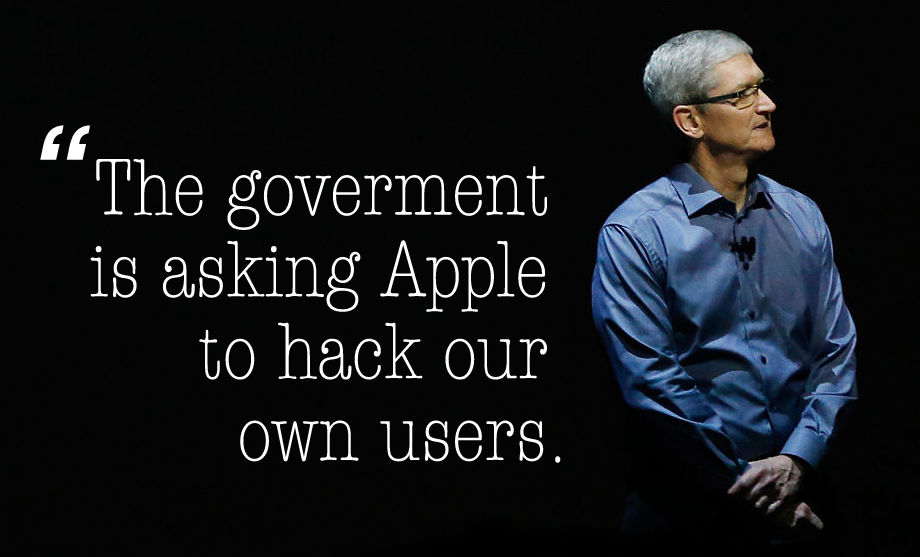
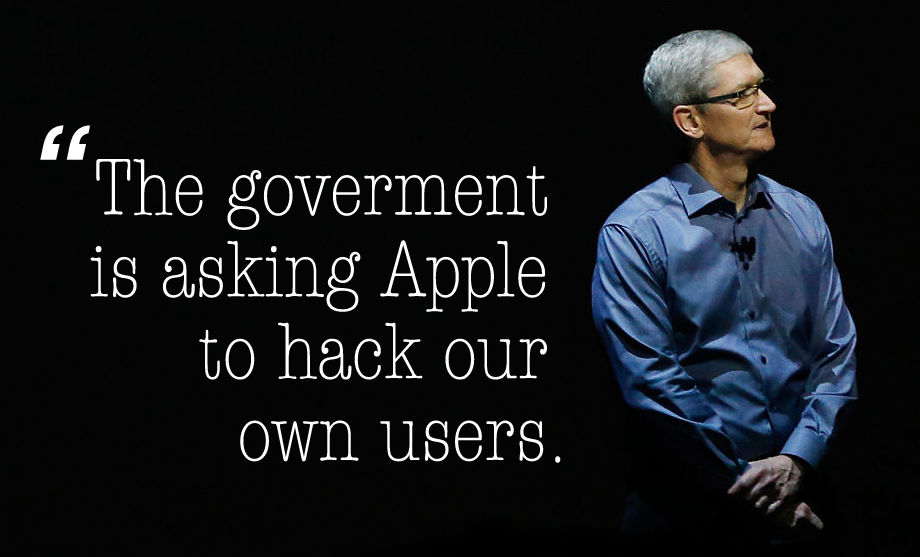 ShortBytes: In response to the Federal court order which was issued to Apple, the maker of iPhone, to help the FBI hack iPhone of one of the San Bernardino shooters, Apple CEO Tim Cook has responded very strongly saying that it would set a “dangerous precedent.”
ShortBytes: In response to the Federal court order which was issued to Apple, the maker of iPhone, to help the FBI hack iPhone of one of the San Bernardino shooters, Apple CEO Tim Cook has responded very strongly saying that it would set a “dangerous precedent.”
Tim Cook’s response came just within 24 hours after U.S. Magistrate Judge Sheri Pym, ruled that Apple must provide “reasonable technical assistance” to the FBI in its efforts to unlock data on Syed Rizwan Farook’s iPhone 5C. If Apple decided to help the investigators that would mean bypassing some of the iPhone’ security features and they include bypassing an auto-erase feature and passcode protection.
Tim Cook has already asserted that the company has helped the FBI wherever it was possible for them. But in the matter of creating a “backdoor” to its operating system, Tim cook has an explanation. Here is an excerpt from the same.
In today’s digital world, the ‘key’ to an encrypted system is a piece of information that unlocks the data, and it is only as secure as the protections around it. Once the information is known, or a way to bypass the code is revealed, the encryption can be defeated by anyone with that knowledge. The government suggests this tool could only be used once, on one phone. But that’s simply not true.
Once created, the technique could be used over and over again, on any number of devices. In the physical world, it would be the equivalent of a master key, capable of opening hundreds of millions of locks — from restaurants and banks to stores and homes. No reasonable person would find that acceptable.
What is your opinion on this? Should FBI be given ‘Backdoor’ access to the iPhone? Or they should ask the ‘Owner’ not the ‘Maker’?
Also read: Ex-NSA Chief Defends End-to-End Encryption. Isn’t It Surprising?