Critical PGP Flaws Can Expose Encrypted Emails In “Plaintext” — Disable It Right Now

Email users who use PGP (based on OpenPGP) and S/MIME to encrypt and decrypt their communications are at “immediate risk.” The reason is that a team of European researchers has found critical flaws in the encryption standards and currently there are no fixes available.
The vulnerabilities dubbed EFAIL are harmful as they can reveal the contents of messages in plain text, even for the messages from the past.
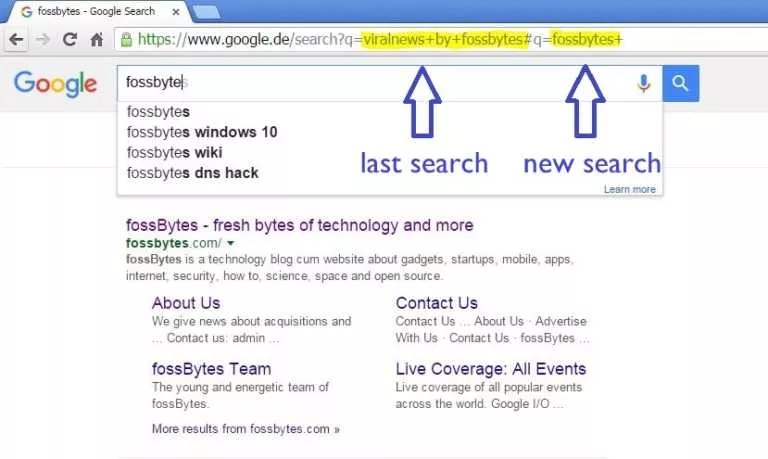
If an attacker gains access to a victim’s encrypted emails through methods like eavesdropping or compromising email accounts, EFAIL can be used to “abuse active content of HTML emails, for example externally loaded images or styles, to exfiltrate plaintext through URLs,” reads the website detailing the vulnerabilities.
We'll publish critical vulnerabilities in PGP/GPG and S/MIME email encryption on 2018-05-15 07:00 UTC. They might reveal the plaintext of encrypted emails, including encrypted emails sent in the past. #efail 1/4
— Sebastian Schinzel @[email protected] (@seecurity) May 14, 2018
A modified encrypted email sent by the attacker to the victim is decrypted by their email client. While doing so, the client loads any external content, thus, exfiltrating the plaintext to the attacker.
The PGP encryption is mostly used by political activists, journalists, and whistleblowers as an extra layer of encryption. On the other hand, S/MIME is used mainly in enterprise infrastructure.
Why this should be taken seriously is because the Electronic Frontier Foundation (EFF) is also spreading the word. The Foundation which has been in communication with the researchers has advised users to “temporarily stop sending and especially reading PGP-encrypted email”.
Disable it right now
Users should immediately disable or remove any tools that automatically decrypt PGP-encrypted emails until the flaws are understood and fixed, EFF said. They have published guides for Thunderbird, Apple Mail, and Outlook.
A more permanent fix requires changes to OpenPGP and S/MIME standards and it is not going to happen overnight. Meanwhile, some vendors are expected to release patches to mitigate EFAIL attacks.
Via EFF
Also Read: Cryptocurrency Mining Malware Found In Ubuntu Snap Store