Cortana Flaw Lets Hackers Access Data, Reset Password On Locked Windows 10 PCs

Security researchers have found a critical flaw in Windows 10 where Cortana can be manipulated into executing Powershell commands on locked devices.
Attackers can misuse this vulnerability to retrieve confidential data, reset the password, log into a device, and even execute codes from above the lock screen. The only sense of satisfaction is that it requires physical access to the device.
Apparently, this hack works even if your PC is locked and encrypted. The reason behind such a massive security hole is the overly helpful behavior of Cortana.
As Cortana relies on indexing for its queries, the researchers found that typing a string of letters, triggers the virtual assistant to bring up many of the files on the system that begin with those exact letters. One can see the full path of the file location and even contents of the file.
How does the exploit work?
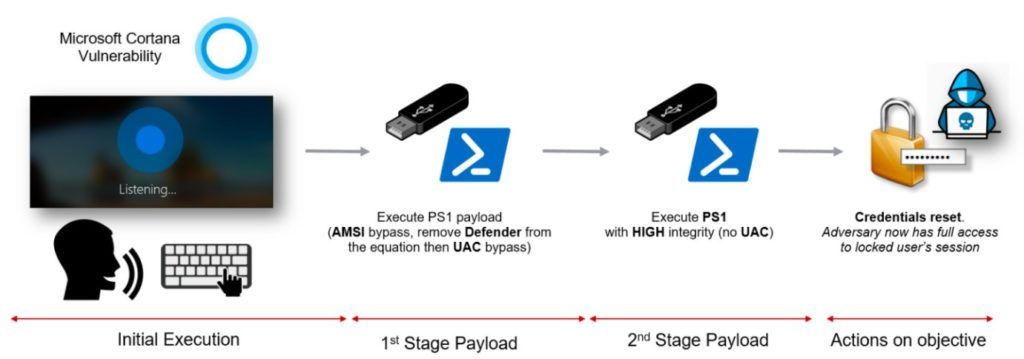 This security flaw was discovered by McAfee which explained the pretty simple trick to ‘break’ into a locked Windows 10 device:
This security flaw was discovered by McAfee which explained the pretty simple trick to ‘break’ into a locked Windows 10 device:
- Activate Cortana through “Tap and Say” or “Hey Cortana”
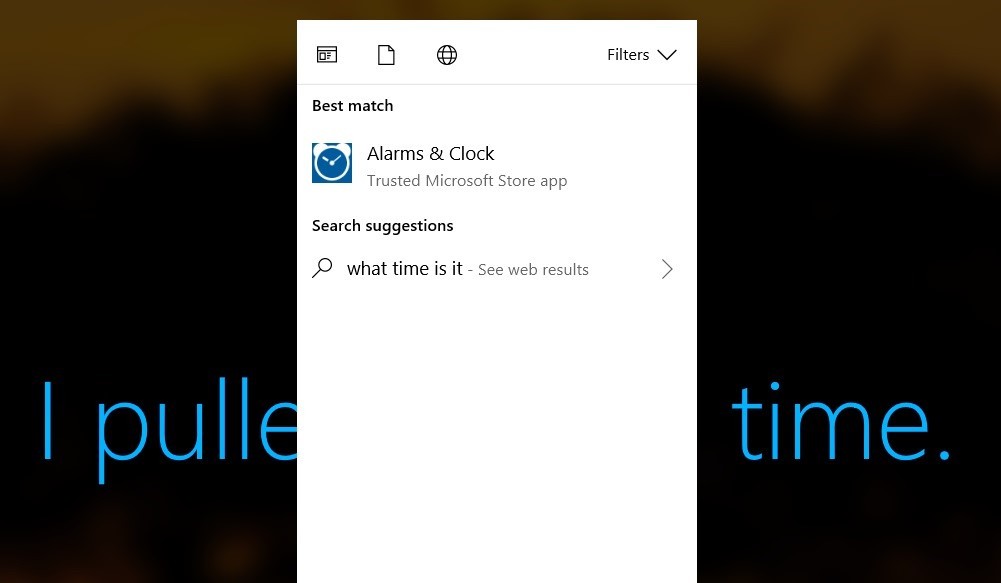
- Ask any simple question, for instance, “What time is it?”
- Press the spacebar, and a context menu will pop up
- Hit Esc and the menu will disappear
- Next, press the spacebar again and the contextual menu will reappear but with an empty search query
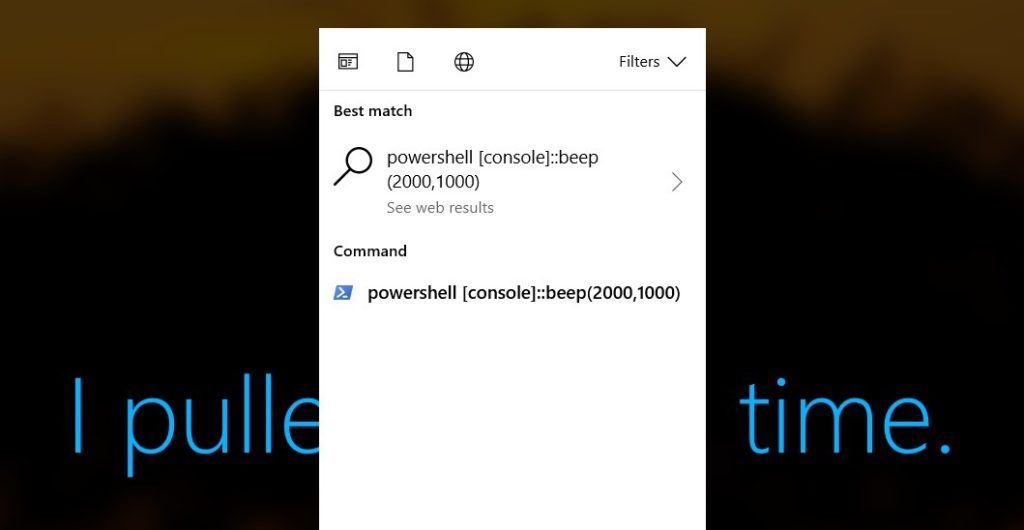
- Start typing but keep in mind that you cannot use backspace. In case you make an error, just hit Esc and start over
- After typing the command, click the entry in the Command list (For this to work, the input must be recognized as a command)
- Right-click and select “Run as Administrator”
The security firm also showed a demo on how this method can be used to reset password and login on a locked Windows 10 device. The only requirement for this method to work is the need for physical access to the system.
The security flaw has been reported to Microsoft and this week’s Patch Tuesday contains fixes (in CVE-2018-8140) for these issues. Users should install the latest security patch to ensure the security of their devices.
Also Read: Microsoft Removes Tech Support For Windows 7, 8.1, IE10, Other Old Product Forums