11 Free And Best Antivirus Software [2021]: Protect Your PC Now

There’s no denying that the internet can sometimes be a hazardous place for PC users, especially Windows users. No operating system, including Linux, is virus/malware-proof; if you’re a Windows user, the odds of your computer getting infected are even higher. To protect your computer from malware, there are a lot of antivirus software out there. In this article, let’s glance at some of the best free antivirus software options out there to help you choose the best one.
“But do antiviruses really help?” Well, the answer is yes and no. If you’re on Windows 10, Windows Defender is more than enough. If you’re on older Windows versions, many free scanners like Bitdefender, Kaspersky, Avast, etc., do a decent job in the best free virus protection. It goes without saying that their paid counterparts offer some premium features and dedicated support. That’s why I’ve also added the links to some notable premium options as well. Do take a look and make sure that your devices are protected from threats in 2021.
Before going ahead, you are also advised to take a look at the list of best Android antivirus apps as well to win at the front of mobile security as well. Did you know that you can also use Command Prompt to remove viruses? To know more, check out the linked article.
What To Look For When Choosing The Best Antivirus Software
Performance, resource consumption, privacy, and features are some of the crucial things to look at when choosing the best Antivirus software. Most of the time, if your PC has way less horsepower, it might lag due to the Antivirus. Hence, choosing a lightweight antivirus is essential.
Most “free” antivirus software is often accused of stealing data from your computer. Hence, read user reviews about the software before installing it. If you want in-depth knowledge about different terms like Malware, Phishing, check out what is the difference: Viruses, Worms, Ransomware, Trojans, Malware, Spyware, Rootkit
- What To Look For When Choosing The Best Antivirus Software
- 11 Best Free Antivirus List For 2021
- 1. Windows Defender
- 2. Avast Free Antivirus
- 3. Bitdefender Antivirus Free Edition
- 4. Avira Free Antivirus
- 5. Kaspersky Free Antivirus
- 6. AVG Free Antivirus
- 7. ZoneAlarm Free Antivirus 2021
- 8. TotalAV
- 9. Sophos Home
- 10. 360 Total Security
- 11. Adaware Antivirus 12
- Editor’s Recommendation: Which Free Antivirus Is The Best?
11 Best Free Antivirus List For 2021
1. Windows Defender
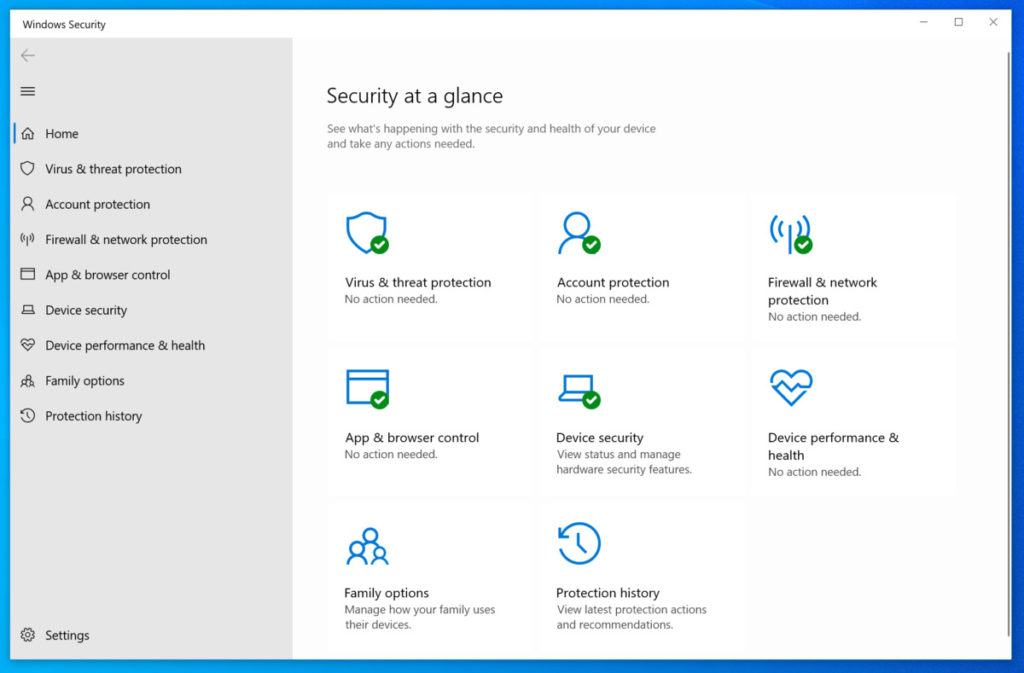
Although Windows Defender was introduced way back in Windows XP, it didn’t do much to protect users other than scanning files and reporting malicious files where some stated that even this feature was broken. Windows Defender was nothing but an application occupying space on their computers until Windows 10.
Apart from the complete revamp, Microsoft has also focused on adding important security features like real-time scanning, Firewall, and Network protection, system performance reports, parental controls, and much more. Above all, it’s completely free and comes built-in in Windows 10.
- Virus and Threat protection actively scans files for Malware and Threats
- Uses Core isolation to protect the core parts of your PC
- Has Domain network, Private network, and Public network firewalls
- It comes with a section to monitor the device’s health like Storage capacity, Battery life, Apps and software, etc.
- Prevents apps from accessing personal data
- Allows you to track your kids’ activities and their digital wellbeing.
Overall, if you’re using Windows 10, you don’t need another antivirus software; Windows Defender should suffice.
Supported platforms
As of today, Microsoft Defender is available only on Windows 10.
Pros:
- No installation needed
- Scans your device in the background
- Digital wellbeing of family integrated
Cons:
- Available only on Windows 10
- Virus scanner is not the best
- Not the most feature-rich software
2. Avast Free Antivirus
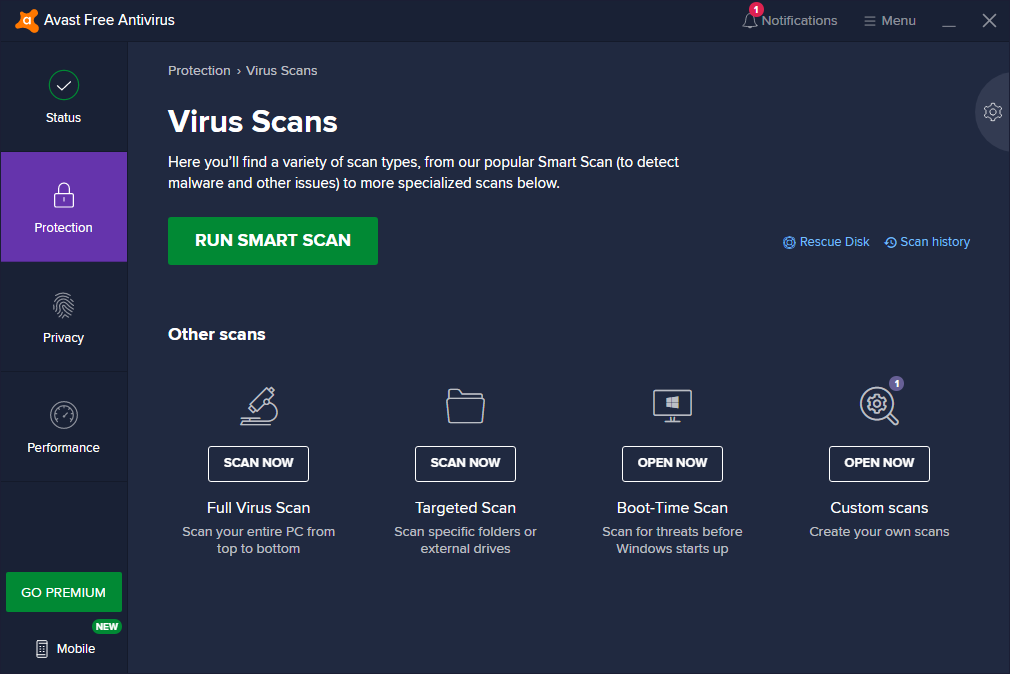
When you’re looking for free antivirus software to maintain the integrity of your computer and save you from different malware and hacking attacks, Avast turns out to be a worthy leader among all solutions. Here are some of the features this software offers.
- This “Intelligent Antivirus” detects malware, viruses, ransomware, and phishing, etc. Using smart analytics, the threats are stopped at the earliest possible time.
- “CyberCapture,” a cloud-based scanner, sends suspicious files for further analysis in the cloud. If it turns out to be a threat, all the users are protected in the future.
- “WiFi Inspector” finds flaws in your home WiFi and makes it more secure.
- “Smart Scan” detects various small-big security holes present on your machine.
- The automatic “Game Mode” makes sure that all notifications are put on hold.
- “Behaviour shield” keeps an eye on the apps and their behavior to make sure that they don’t harm your machine.
Overall, Avast is a feature-rich antivirus compared to other entries on the list, including the famous Bitdefender and Avira Free Antivirus software. You also get a free password manager named Avast Passwords as well. The company claims to include machine-learning-powered protection that learns and improves itself with time. The user interface of this top free antivirus for 2021 is also unlike any other antivirus software that you’ll come across on this list.
The paid antivirus products from Avast also come with added features like ransomware shield, firewall, anti-spam, sandboxing, etc. These features are great for any small startup or home users that wish to ensure all-around protection. It comes with a 30-day free trial, so there’s no harm in giving it a try if you wish to go for extra security layers.
Bear in mind that Avast “Free” antivirus was accused of stealing personal data and selling it to tech firms for millions.
Supported platforms
The best free antivirus software solutions of Avast are available for Windows, Mac, and Android platforms. You can choose them as per your needs from the official website.
Pros:
- The free version includes a lot of features
- Easy to install
- Easy to use and intuitive UI
Cons:
- It tends to slow down the PC
- Blocks websites that are safe
3. Bitdefender Antivirus Free Edition
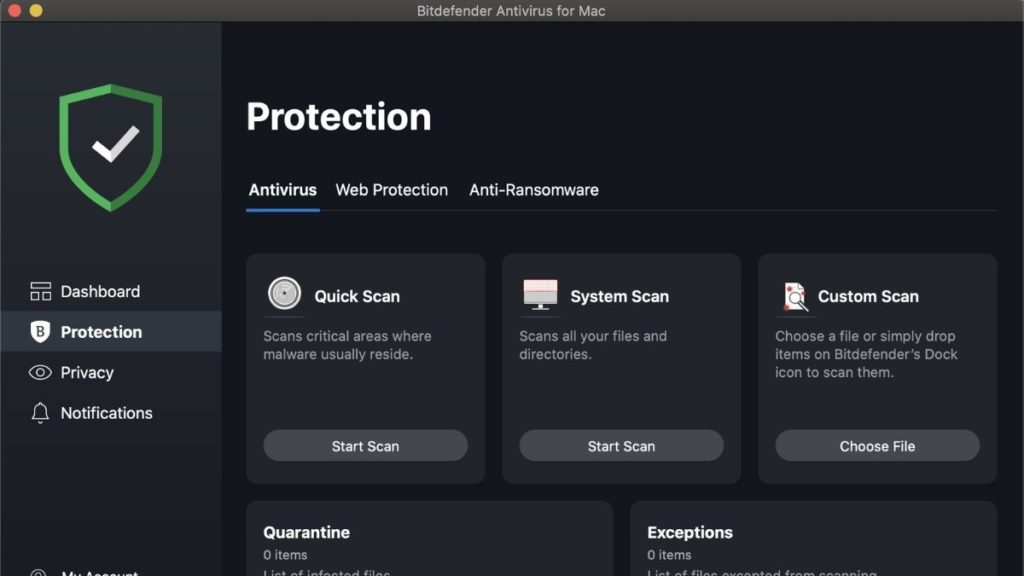
Bitdefender, the Romanian internet security solutions company, doesn’t need any introduction in the cybersecurity world. The company offers top-notch products for home and business use, and Bitdefender Antivirus Free Edition is no exception. It gives a tough competition to Avast’s solution. It’s a no-nonsense, free computer antivirus software that has all the major features you’d expect from a top-rated and free virus protection program. Its chief features include:
- “On-demand virus scanning” ensures removing different kinds of worms, trojans, viruses, ransomware, rootkits, spyware, etc.
- The “anti-phishing feature” lets you protect yourself and take control of your online accounts in the best manner possible.
- With “behavioral detection,” your apps are actively monitored, and instant action is taken.
- The “Anti-fraud” feature warns you when you visit the sites that try to scam you.
In the tests of different independent security labs, Bitdefender Antivirus Free Edition has excelled. This free virus scanner keeps running in the background all the time and comes with an easy-to-use interface. This top antivirus protection for 2021 is also quick to install and light on your device’s resources.
When it comes to Bitdefender free vs. paid comparison, the paid version comes with features like a password manager, browser hardening, specialized ransomware protection, webcam protection, social networking protection, etc. A feature named Bitdefender Autopilot is available to take care of the entire cybersecurity on its own. The plan also comes bundled with VPN protection for added security and safety while browsing the web. If that sounds like what you need, give it a go, as it also comes with a 30-day free trial.
Supported Devices
It’s a cross-platform product that is supported by Windows, macOS, and Android. Windows users can install it on Windows 7, Windows 8, Windows 8.1, and Windows 10.
Pros:
- Same virus scanner as the paid version
- Accurately blocks malicious websites
Cons:
- Advanced malware protection is absent
4. Avira Free Antivirus
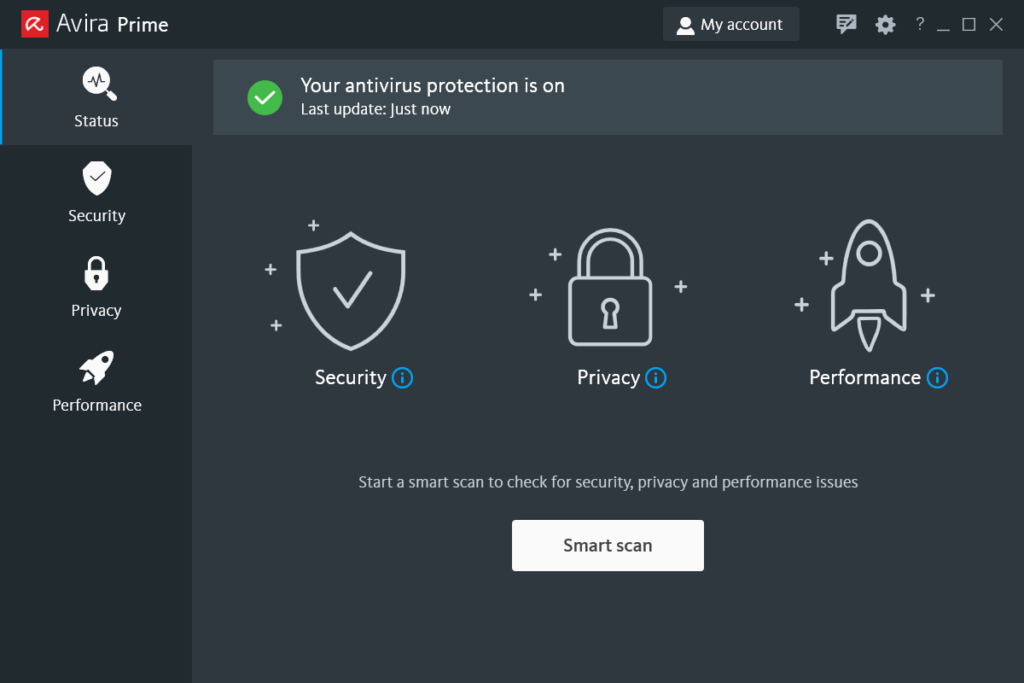
Making its first appearence on the horizon of PC protection in 1986, Avira has also been performing well in the test of different independent cybersecurity labs. While it might not be as feature-packed as Avast Free Antivirus, Avira is known to turn out to deliver a solid performance with a clean user interface. The new 2021 version labels itself to be very lightweight, up-to-date software. Some of the most noticeable features of Avira’s free solution are:
- Avira’s “Protection Cloud” is an early warning system that analyzes the unknown files in clouds and protects the community in real-time.
- Its antivirus scanner takes care of most types of malware, including virus, worm, trojan, ransomware, etc.
- With the help of the Avira Browser Safety extension, you get added features like Browser Tracking Blocker, Safe Browsing, and Price Comparison.
- The “PUA Shield” stops unwanted apps from harming your system.
The Protection Cloud of Avira uploads the digital fingerprint of the malicious file to the cloud and checks the same against the company’s database. Based on the detection results, it takes further action.
Supported Platforms
Avira Free Antivirus software is available for all popular platforms, including Windows, Mac, iOS, and Android.
Pros:
- Lightweight and easy on PCs with fewer resources
- The free version comes with lots of features
Cons:
- Lots of pop up ads
- File scanner isn’t the best
5. Kaspersky Free Antivirus
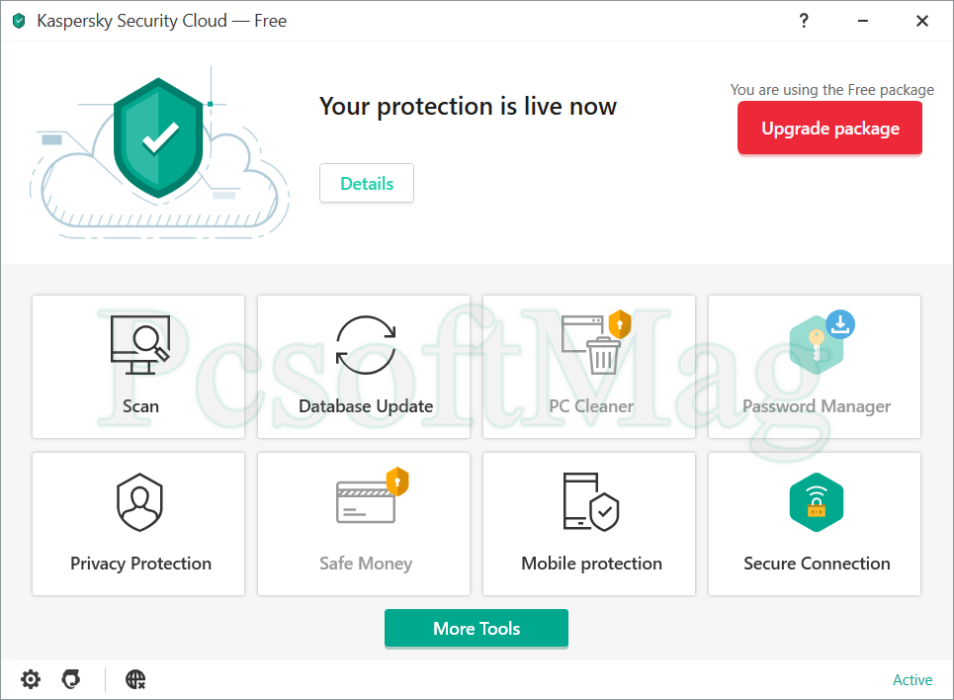
It wasn’t long ago when Russian cybersecurity leaders Kaspersky Labs launched a full-fledged free cybersecurity suite. The company’s home and enterprise products are frequently featured on the annual top 10 antivirus software lists of different websites and experts. The free and lightweight antivirus from Kaspersky Labs is a basic program that doesn’t come with fancy features and promises to do its job with diligence.
Talking about its features, you get the core protection of this not-so-heavy antivirus, including protection against dangerous malware, viruses, phishing attacks, spyware, etc. Its web protection also makes sure that notorious websites won’t fool you, and you also get email protection. You can go for the paid version’s trial if you need advanced features like cross-platform protection, safe online transactions, kids security, password manager, etc.
Supported Platforms
Kaspersky Free Antivirus is only available for the Windows platform. Android users can go from Kaspersky Internet Security, whose basic version is free.
Pros:
- Great Phishing protection
- Blocks malware very well
- Is available for Android and iOS as well
Cons:
- None
6. AVG Free Antivirus
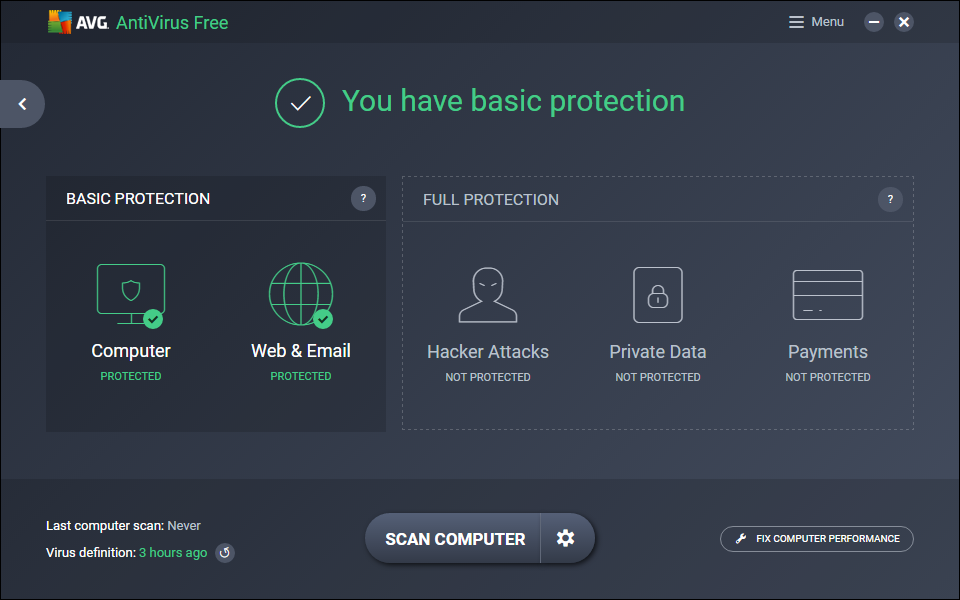
In September 2016, Avast Software completed the acquisition of AVG Technologies. While both these companies enjoy an enviable reputation in the cybersecurity business, Avast is more popular in non-English speaking markets. After the merger, both the products have maintained their look, and we can expect to see some technical under-the-hood improvements in both the products. AVG Free Antivirus is AVG’s popular free virus scanner program that continues to get better.
The main features of the AVG Free Antivirus are:
- Complete virus scan and protection from different malware types, including viruses, spyware, ransomware, etc.
- Web protection to keep you safe from unsafe downloads and links. Email scanning is included as well.
- It also scans your system for performance issues and notifies you of the same.
- Real-time security updates are also provided.
Apart from protecting from malware and harmful programs, you also get a 30-day trial of the free AVG VPN tool. However, if you’re looking for a dedicated VPN to safeguard your privacy, we recommend you go for the likes of PIA or ExpressVPN.
A special feature of this security tool is the inbuilt File Shredder feature that lets you shred content with AVG and get rid of it completely. You can use this feature by directly right-clicking on Recycle Bin or individual files/folders. This top antivirus software of 2021 also features a neat and clean interface that makes it easy for the users to use the tool with ease and fix their computer’s performance issues effectively.
While these features of one of the best free antivirus should be enough for most users, AVG also providers more paid options in the form of AVG Internet Security (free trial available) and AVG Ultimate. These options ensure dedicated support, Firewall, and Pro apps for mobile. AVG Internet Security also lets you create personal folders that come with an added layer of ransomware protection.
Supported Platforms
AVG Free Antivirus software is available both for Microsoft Windows and macOS platforms. For Android users, there’s a free option in the form of AVG Antivirus for Android.
Pros:
- Comes with a decent amount of useful features
- Malware scanning is accurate
Cons:
- Could reduce the boot times significantly
7. ZoneAlarm Free Antivirus 2021
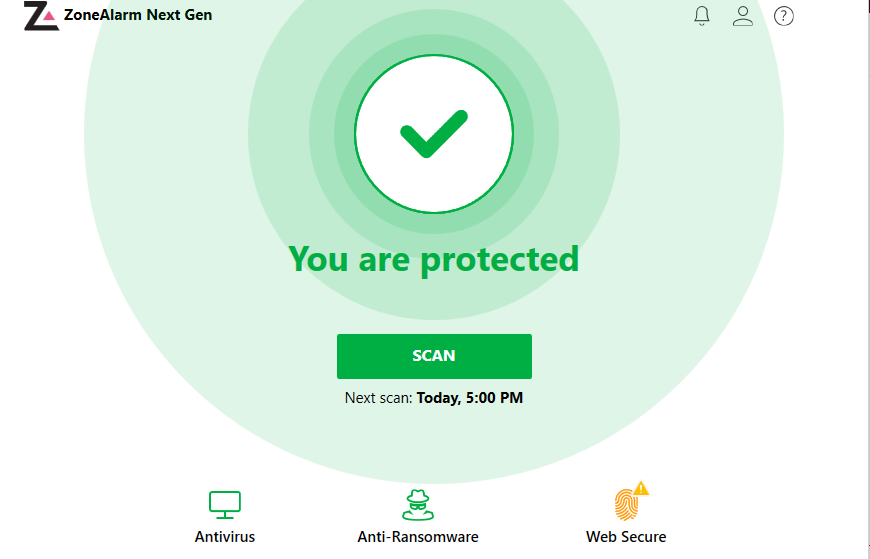
CheckPoint’s ZoneAlarm Free Antivirus was earlier called ZoneAlarm Free Antivirus + Firewall. The company has renamed this product but retained the firewall feature, making it a top recommendation on this top 10 antivirus list for 2021. Let’s take a look at its major features:
- Antivirus and Antispyware for getting rid of viruses, spyware, bots, worms, trojans, and other threats. You also get protection from spyware that infects the system via various online attack vectors.
- Personal Firewall that keeps an eye on incoming and outgoing traffic and protects your PC.
- Customizable scanning modes to run the scan as per your need.
- Gamer mode for gaming sessions without interruptions.
- Real-time security updates and daily credit monitoring.
- The Web Secure free Chrome extension warns you about malicious websites so that you could be extra careful while downloading or uploading your favorite files.
This recommended antivirus software for malware protection makes sure that your computer is extra secure with real-time security updates. It allows the tool to respond quickly to breaking threats and information from millions of users.
ZoneAlarm’s Free Antivirus is recommended if you wish to couple the advantage of antivirus with a firewall. If you’re looking just for a firewall, ZoneAlarm has a separate free program for that. If you’re only looking for the best free antivirus, choose Kaspersky’s offering as ZoneAlarm uses antivirus technology licensed by Kaspersky.
The company also ships a premium security product called ZoneAlarm Extreme Security. It protects you from identity theft, phishing, zero-day attacks, etc. You also get the facility of online backup, laptop tracking, identity protection, and family protection.
Supported Platforms
ZoneAlarm Free Antivirus is available for Microsoft Windows operating system, with support for Windows 10/8/7.
Pros:
- Protection feature is taken from Kaspersky
- Introduces two-way firewall
Cons:
- Lacks typical antivirus features
8. TotalAV
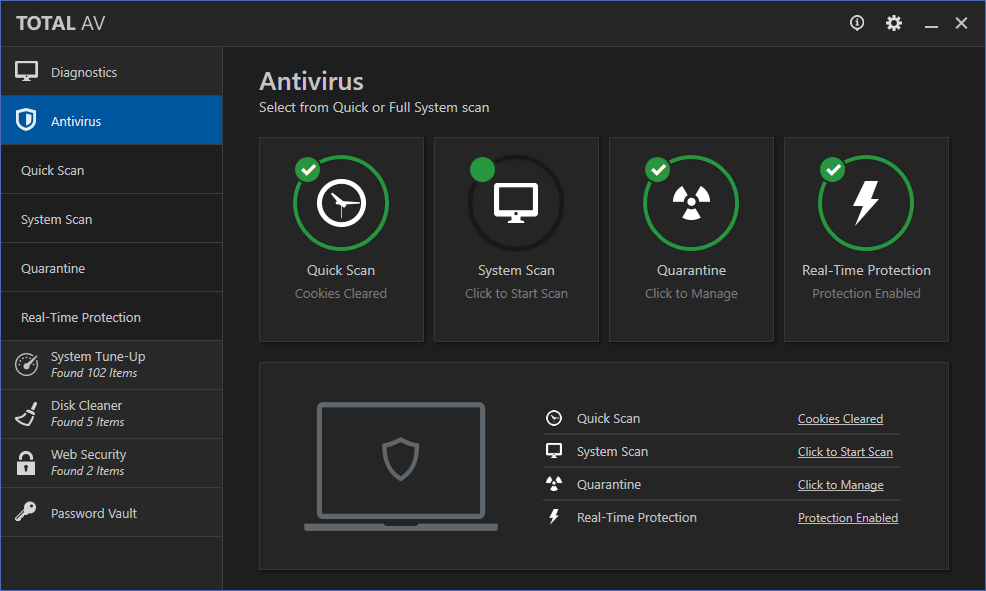
TotalAV is a cloud-based antivirus program that is based on Avira’s scanning engine. The free version of this antivirus software provides the following features.
- All the work is done in the cloud to make it a lightweight antivirus.
- Internet Security: Block shady URLs and protect your PC
- Extensive Virus Definitions provide enhanced protection
- You can protect your identity using the Data Breach Monitoring feature
Overall, TotalAV is definitely one of the best free antivirus software out there.
The premium version, also known as TotaAV premium, introduces more features like VPN, remote firewall, disk cleaner, cloud scanning, ad blocker, and a lot more.
Supported Platforms
TotalAV is available only on the Windows platform.
Pros:
- Protection against malicious URLs
- Speedy scans
- User-friendly and easy to install
Cons:
- Doesn’t provide as many features as other antiviruses on this list
9. Sophos Home
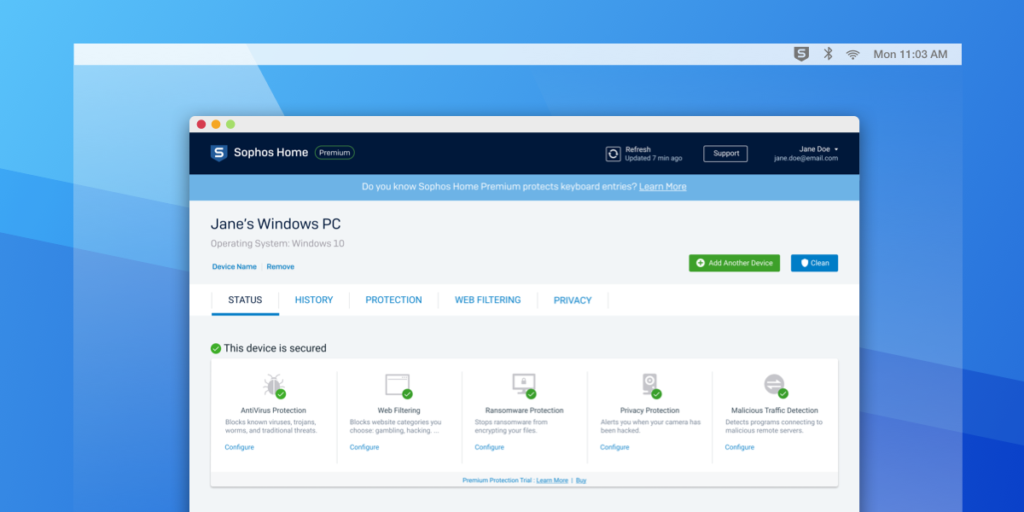
Sophos is another reputable name in the cybersecurity world. Their Sophos Home free antivirus solution promises best-in-class protection from tons of threats that keep budding to take control of your digital lives. This top-rated antivirus software has repeatedly scored good grades in tests of independent labs. Here are its major features:
- Advanced computer security to remove malware, ransomware, viruses, apps, and programs to keep your machine clean.
- Using SophosLabs’ real-time threat intelligence, the behavior and activities of programs and files are analyzed continuously.
- Lots of bonus features coupled with basic computer security.
- Clean interface and easy installation.
As said above, the Sophos Home PC protection program has many added features that might interest you. It prevents your computer from connecting to malicious websites that are a source of spyware and other malware. You also have the power to control the content your family accesses. Moreover, you can also control it from any web browser remotely.
Supported Platforms
Sophos Home supports Windows as well as macOS operating systems. You can install it on Windows 7, 8, 8.1, and 10. Apple users can run it on OS X 10.10 and later.
Pros:
- Gold standard in malware scanning
- Protects against malicious websites
Cons:
- Badly implemented parental control feature
10. 360 Total Security
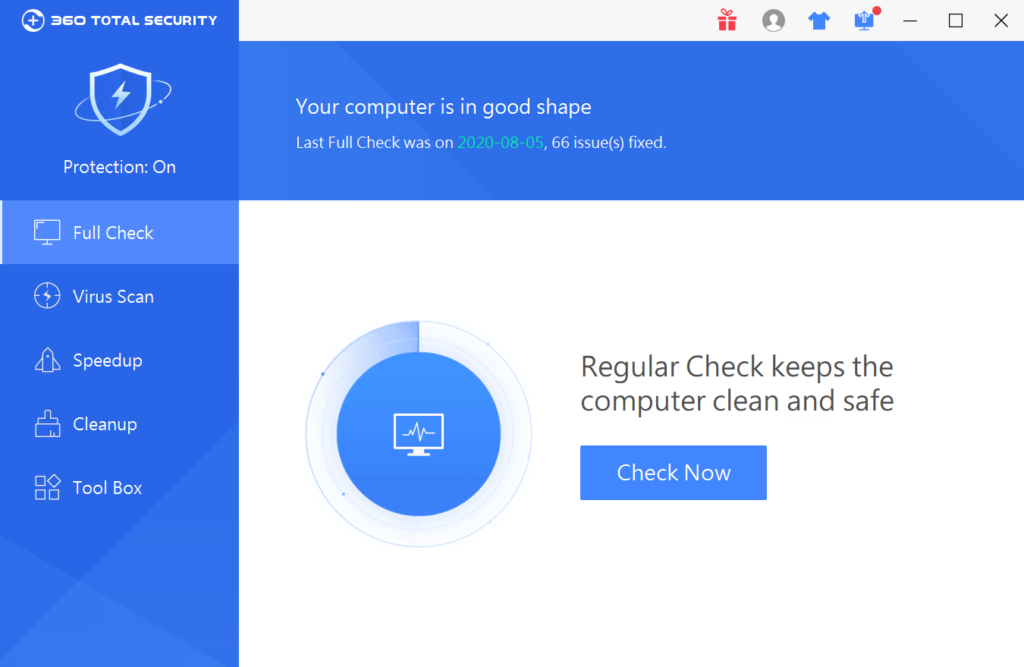
If you’re looking for feature-rich antivirus software that doesn’t cost you a penny, you can give Qihoo’s 360 Total Security a try. A big highlight of this free antivirus is the licensed Bitdefender and Avira antivirus engine. The other features of 360 Total Security are:
- Web protection includes downloaded file scan, website blocking, and shopping protection
- Auto-scanning of files when saved or opened.
- Sandboxing and system clean-up feature
- Anti-ransomware to protect you from the increasing threat of recent times.
While its core protection might not beat the market leaders, 360 Total Security is one feature-rich software. Apart from the features mentioned above, you get webcam protection, keylogger blocking, USB drive protection, file system and registry protection, network threat blocking, and more. So, if you love options to play with, give it a try.
Supported Platforms
This security software from Qihoo is available for Microsoft Windows operating system.
Pros:
- Easy to use
- It doesn’t consume a lot of system resources
- Nice interface
Cons:
- Too many ads
- Tools aren’t so good
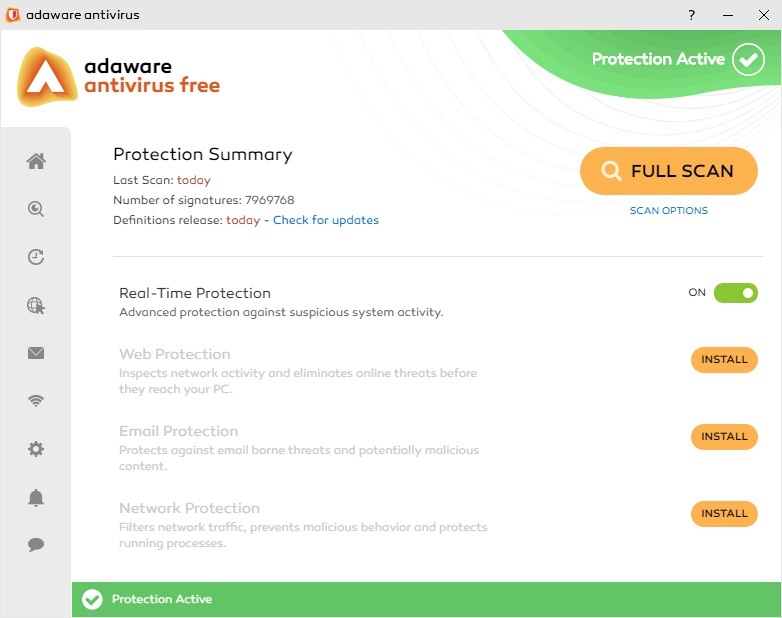
11. Adaware Antivirus 12
Adaware antivirus was earlier known as Ad-Aware from Lavasoft. This free antivirus software for PC has undergone an overhauling and rebranding. While it might not be the best virus protection you can get for your PC, a few highlight features of Adaware antivirus are worth mentioning:
- Protects your PC from popular threats like spyware, viruses, worm, trojans, etc.
- Download protection scans all the files that you download from the web.
- The files and processes are scanned and blocked in real-time.
- Blocks your Camera and Microphone to ensure no one’s sneaking on you
- It comes with a cleaner and driver manager
While most of the free computer protection software on this list had some bonus features to offer, Adaware antivirus 12 doesn’t have any. As it’s free, you can give it a try. Still, I’ll recommend you go for the top picks like Kaspersky, Avast, or Bitdefender.
Supported Platforms
You can install Adaware Antivirus 12 on Windows 10, 8, 8.1, and 7.
Pros:
- Malware scanner is decent
Cons:
- No protection against malicious websites
- Lacks many antivirus features
Editor’s Recommendation: Which Free Antivirus Is The Best?
Viruses, trojans, malware are something that every PC user should know and know how to tackle. When it comes to delivering the expected performance without taking any money from the users, few deliver. That’s why it’s essential to choose the best free software protection by analyzing all the aspects.
Out of these top-ranked best free antivirus software for 2021, I’d suggest you go with Avast Free Antivirus or Bitdefender Free Antivirus. Avast has many bonus features bundled with its free software, and it should attract many users. Bitdefender’s software follows a no-nonsense principle and detects threats with ease. So, depending on your personal choice, you can select any of these.
FAQs on antivirus solutions
Yes, the free version of Avast is completely free, and there are no hidden charges. However, there is a paid version too that offers extra features.
It depends on which antivirus software you’re using. There’s no “jack of all trades” kind of antivirus software, but most of them do help you stay protected from Viruses, trojans, and malicious websites.
Sadly, no antivirus is “completely free.” At the end of the day, these software manufacturers are companies that are here to earn. Hence, in most antiviruses, you miss out on features that are only available in premium versions.