SambaCry: This Linux Malware Is Turning Machines Into CryptoCurrency Miners
Short Bytes: A few weeks ago, we got to know about a vulnerability that dealt with all versions of Samba. While a patch was released to fix this SMB protocol issue, researchers have managed to record the attacks using this flaw to target Linux machines and mine monero cryptocurrency. The SambaCry malware spreads by scanning for Raspberry Pi devices with open SSH port and unchanged ‘pi’ user password.
Over the last few weeks, WannaCry ransomware had managed to haunt the users of outdated Windows OS. This has also inspired the Linux users to share memes which roasted Windows users. They assumed that the words Linux and malware don’t go hand in hand.But, a new malware named Linux.MulDrop.14 has managed to target the Raspberry users who haven’t changed the default passwords of their devices. This vulnerability is exploiting an earlier reported Samba vulnerability.
Recommended: 8 Best Anti Ransomware Tools You Must Be Using In 2017
Targeting the older versions of Rasbian OS, the Linux.MulDrop.14 is a Linux Trojan. It’s a bash script that contains a cryptocurrency mining program, which is compressed using gzip and base 64 encryption.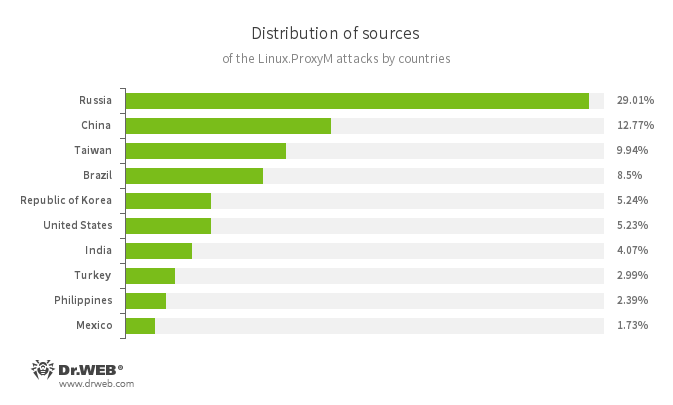
After infecting the Raspberry Pi-powered devices, the cryptocurrency program is launched. Further, the bash script installs libraries needs for mining cryptocurrency. As this malware was uncovered close to WannaCry outbreak, it’s being termed as EternalRed or SambaCry.
“In an infinite loop, using zmap, the Trojan searches for network nodes with an open port 22, after that it uses sshpass to log into them with the following login:password pair: pi:raspberry, and then—to save and run its copy,” malware’s description on Dr. Web’s website says.
According to the Secure List researchers, SambaCry runs the open source miner utility cpuminer (miderd). The cryptocurrency being mined here is monero.
The actions of malware came into the limelight after a Samba patch was released, which concerned with all versions released since 2010. Using the same flaw that can be exploited using SMB protocol, a hacker can open a pipe on Samba servers and execute malicious code remotely.
At the moment, the actual scale of this malware infection is unknown. But, this news must warn sys admins to update their Samba software and make their systems immune to such attacks.
You can find more information about the SambaCry attack on Secure List blog.
Also Read: WannaLocker — A New WannaCry-inspired Ransomware Is Attacking Android Smartphones






