Websites Can Now Track 36 Features Of Your Computer, Identify You Even If You Use Multiple Browsers

Short Bytes: A new research conducted at the Lehigh University has taken the browser fingerprinting to a whole new level. They have devised a method to create a digital fingerprint and identify 99.24% users, regardless of the web browser they are using. For this, they take various hardware and software features of the users’ device into consideration that are independent of any specific web browser.
Almost every website we visit tracks us in some or the other form. They take the advantage of a thing known as Fingerprinting. In this, a digital fingerprint (a unique set of information) of the user’s web browser is generated. Among various things, it usually contains time zone information, various settings, and tells if Do Not Track is enabled or not. But this fingerprint is confined to a single wOeb browser. If a person starts using another browser on their computer, things might not be the same.A team of researchers led by Yinzhi Cao, an assistant professor at the Lehigh University, has developed a new browser fingerprinting technique which enables a website to track users regardless of what web browser they are using.
“Our approach utilizes many novel OS and hardware level features, such as those from graphics cards, CPU, and installed writing scripts,” reads the research paper titled (Cross-)Browser Fingerprinting via OS and Hardware Level Features. “We extract these features by asking browsers to perform tasks that rely on corresponding OS and hardware functionalities.”
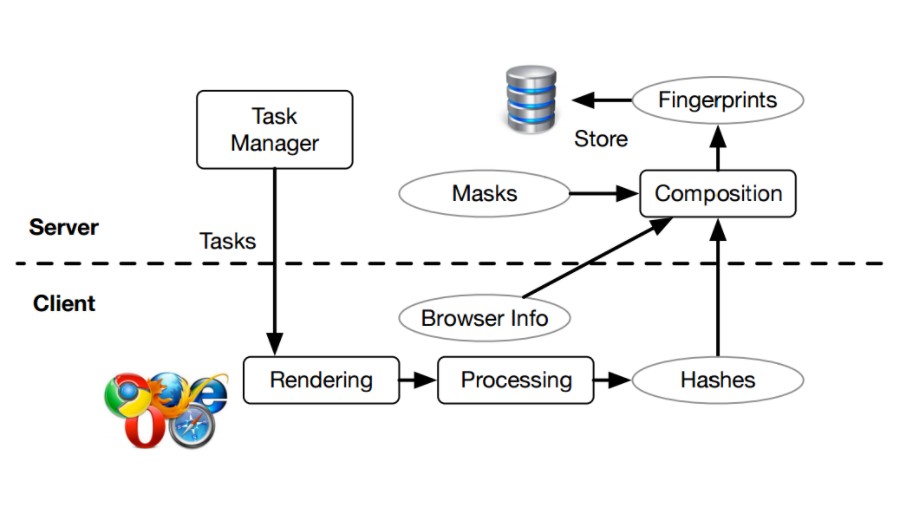
The browser fingerprint created as per their technique take 36 cross-browser features into consideration. These features are not confined to one specific web browser on the machine.
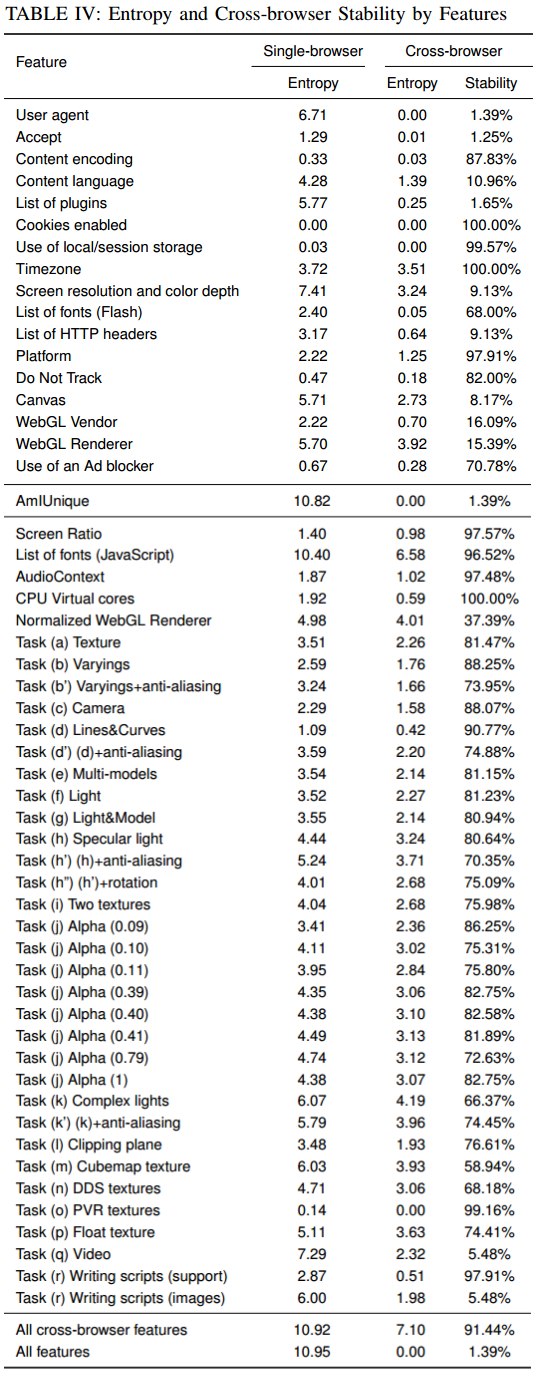
After analyzing their cross-browser fingerprinting technique on a given dataset, the team was able to detect around 99.24% users. The results were better when compared with the numbers of AmIUnique, a single fingerprinting technique, which was able to detect 90.84% users. They have created an experimental website where you can check the uniqueness of your machine. You can find the source code of the researchers’ cross-browser fingerprinting technique here.
Browser fingerprinting shouldn’t be viewed with a bad filter in between. It helps websites to cater relevant content to users on the basis of their device hardware and location details and other things. It can be used to identify them on the internet. Hence, protective measures should be taken.
A sense of relief is that cross-browser fingerprinting isn’t a thing you would find every other website. Even Cao isn’t aware of any website using the technique to track users and their devices. Tor browser can provide a tracking-less environment when techniques like this exist.
Did you check your cross-browser fingerprint? Drop your thoughts and feedback.
Also Read: 10 Things Google Knows About You That You Probably Didn’t Know