Even Batteries Can Be Used To Steal Data From Your Smartphone

A new research has proved that the battery in your cell phone could be turned into a secret surveillance device which can potentially leak sensitive information.
Researchers explained in their paper how malicious batteries in smartphones could be used to read everything you type on your phone just by analyzing the battery power levels.
Batteries used in modern smartphones have the ability to monitor power consumption from apps to prolong battery life by managing the resources and improve the responsiveness of a device.
This ability is gained by creating a communicating channel between the phone’s hardware and software through Battery Status API. This API can be manipulated to capture the sensitive information remotely.
The “attack” could take place by replacing the battery of a target smartphone with a compromised one. This could be done by gaining physical access to the device or by selling such malicious batteries to resellers for battery replacement.
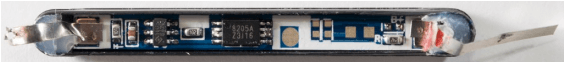
The malicious batteries are implanted with a micro-controller that can record both inward and outward power flow of the device.
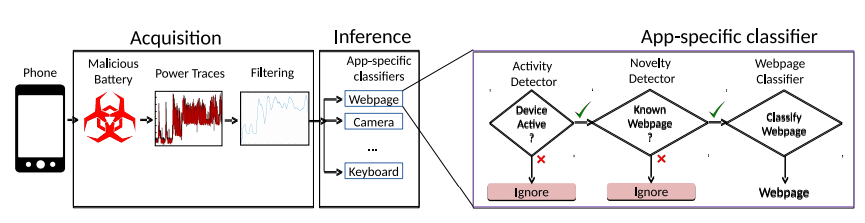
The next step includes leveraging the Battery Status API by accessing through a vulnerable browser like Chrome and captured data could be sent to a malicious website.
Data captured with the help of micro-controller and Battery Status API could be analyzed with the help of an AI to match power flows with specific keystrokes and pinpoint the characters typed on the keyboard.
This method can allow hackers to do the following:
- infer characters typed on a touchscreen
- accurately recover browsing history
- detect incoming calls
- check metadata of photos including their lighting conditions
At present, Chrome is the only “vulnerable” channel through which the attack can be conducted. Browsers like Mozilla and Safari have already revoked support for the Battery Status API.
Fortunately, no such real-world attack has been registered yet, and the attack remains theoretical for now.
Also Read: WPA3: Wi-Fi Receives Its Biggest Security Upgrade After 14 Years