Here’s How To Disable Print Spooler To Fix Windows Printer Vulnerability

Microsoft just discovered another windows printer vulnerability (CVE-2021-34481) that could be exploited by hackers. This comes right after the company released a security patch this month to fix the PrintNightmare Flaw. This new vulnerability allows hackers to install programs; view, change, or delete data; and create new accounts on your PC.
However, an attacker must have the physical access to execute code on a target system to exploit this vulnerability. There’s no telling when this flaw will be patched, but there is a temporary workaround for those who might be concerned. The workaround for this vulnerability is stopping and disabling the Print Spooler service, as suggested by Microsoft in its security advisory.
How to disable the Print Spooler service to fix printer vulnerability?
Option 1 (PowerShell)
You would not be able to print locally or remotely after turning off the Print Spooler service. However, your device should be protected against PrintNightmare or any other printer vulnerability attack.
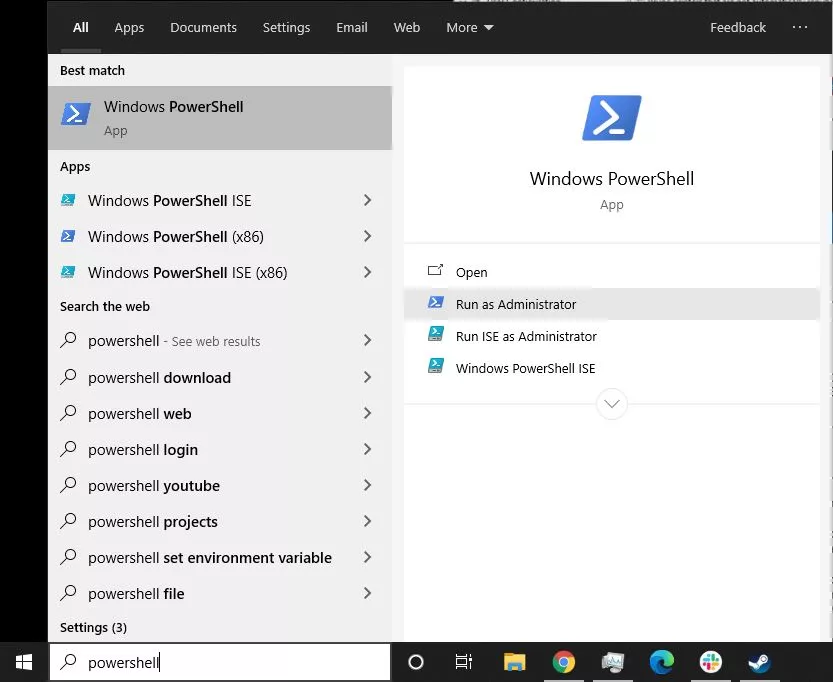
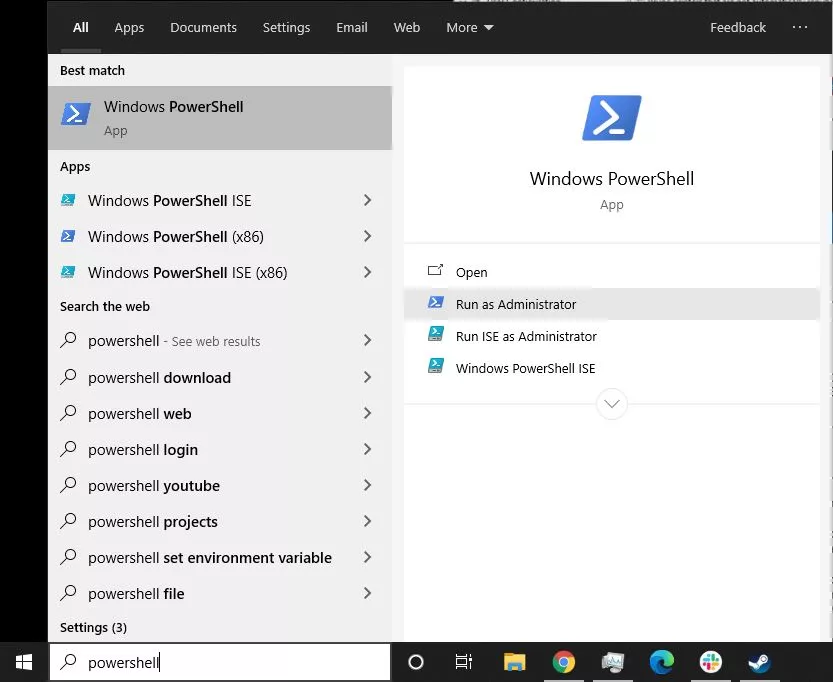
1. Search for PowerShell in the Start Menu and run the program as an administrator.
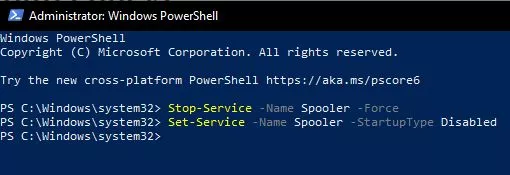
2. Type in the following command to stop the Print Spooler service and press Enter.
Stop-Service -Name Spooler -Force
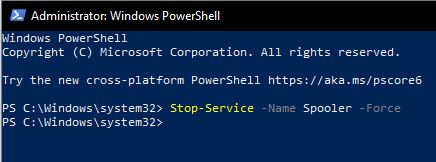
3. Type in the following command to prevent the service from starting back up again during restart and press Enter.
Set-Service -Name Spooler -StartupType Disabled
Option 2 (Group Policy)
By doing this, the printer directly connected to the device will continue to work but won’t work remotely. This is what I would recommend, as most hackers tend to use these kinds of vulnerabilities remotely. However, this method won’t work for Windows 10 Home users.
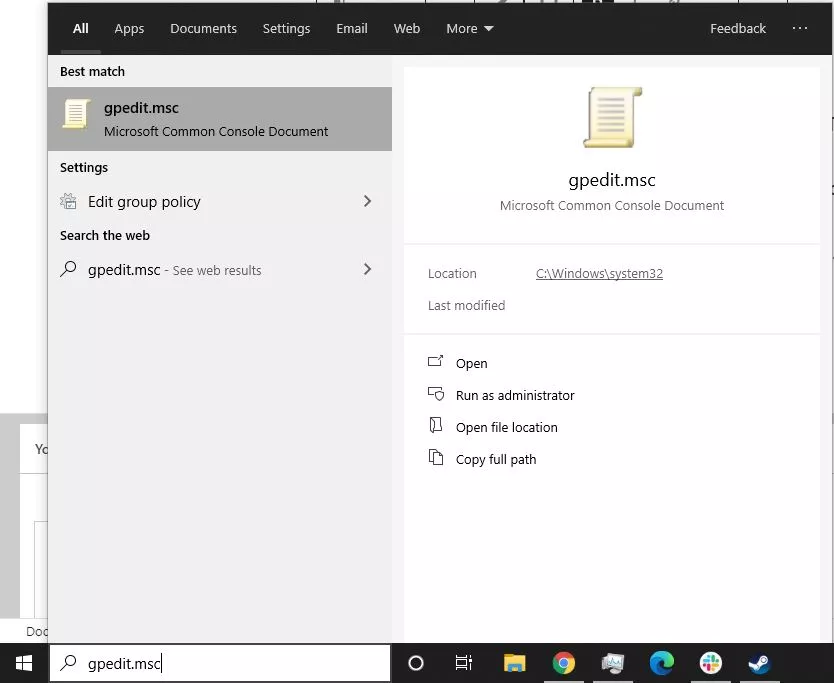
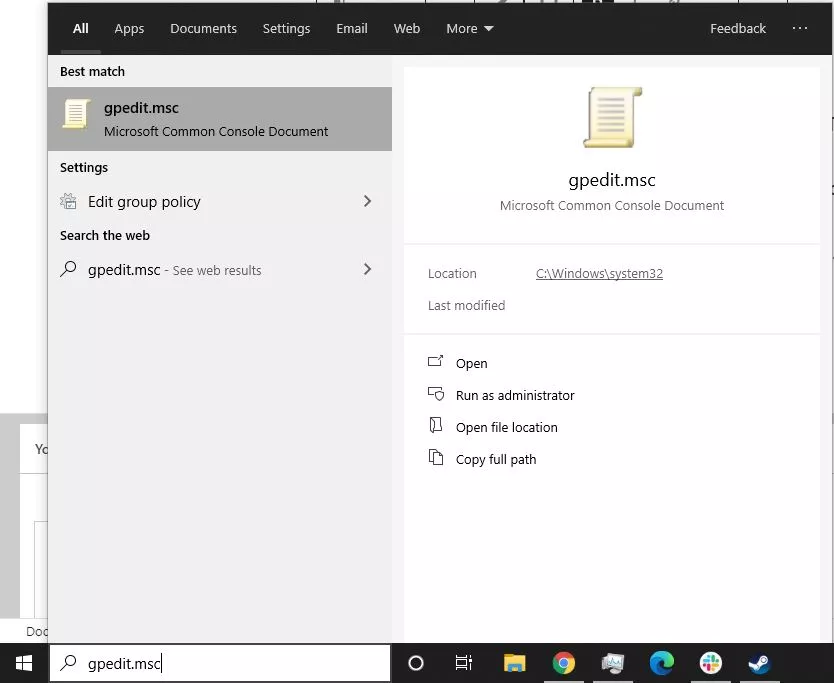
1. Open Start and search for gpedit.msc.
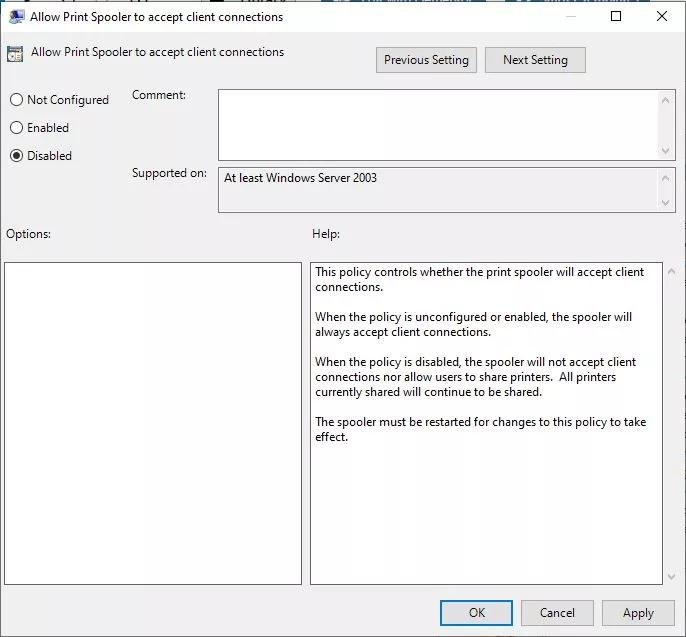
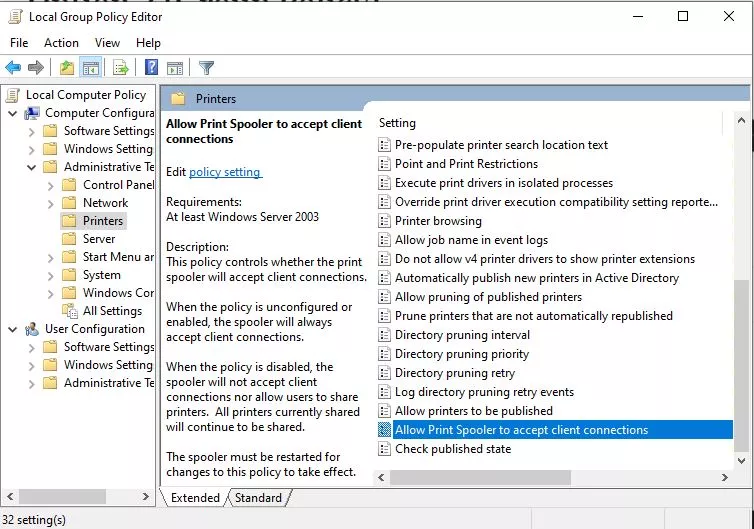
2. Now go to Computer Configuration > Administrative Templates > Printers. Scroll down and double-click the Allow Print Spooler to accept client connections.
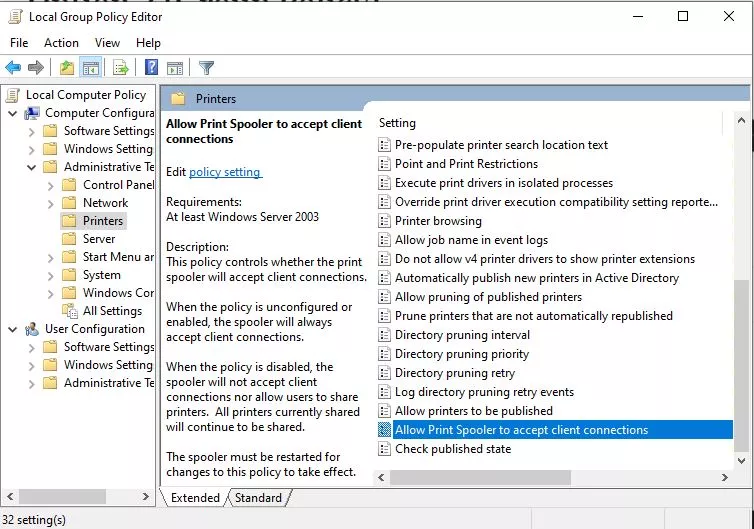
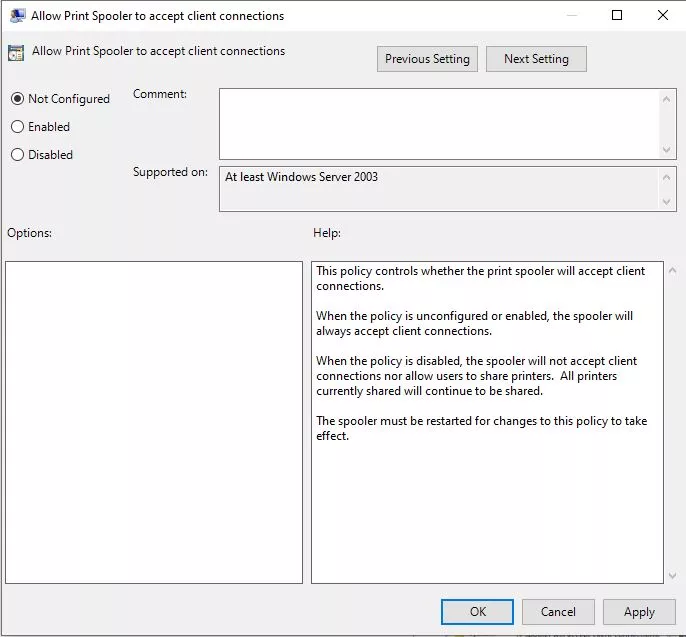
3. Select the Disabled option, click Apply, then OK.
How to re-enable the Print Spooler service after a fix for printer vulnerability?
Once Microsoft fixes this issue with a security patch, you can enable your Print Spooler service using the same method you disabled it.
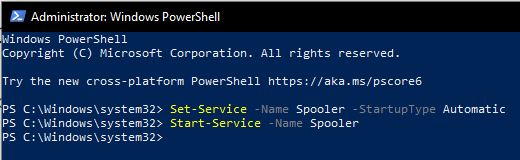
Option 1 (PowerShell)
1. Search for PowerShell and run the program as an administrator.
2. Type in the following command to stop the Print Spooler service and press Enter.
Set-Service -Name Spooler -StartupType Automatic
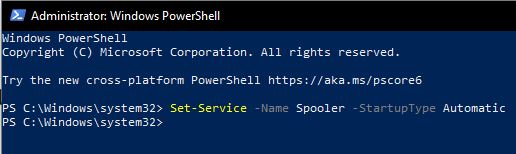
3. Type in the following command to start the Print Spooler service and press Enter.
Start-Service -Name Spooler
Option 2 (Group Policy)
1. Open Start and search for gpedit.msc.
2. Now go to Computer Configuration > Administrative Templates > Printers. Scroll down and double-click the Allow Print Spooler to accept client connections.
3. Select the Not Configured option, click Apply, then OK.
Just like the case of PrintNightmare, until a security patch is released, this is the only known method by which people can secure their devices. Until then, make sure to take care of this Microsoft Windows vulnerability by using this workaround.