AMD Processors Flaws: Firmware Patches Coming Soon, Won’t Affect Performance

Last week, the Isreal-based security company CTS labs was trending in the news for disclosing 13 critical vulnerabilities in AMD’s Ryzen and Epyc processors–only to be slammed by Linus Torvalds and many other people.
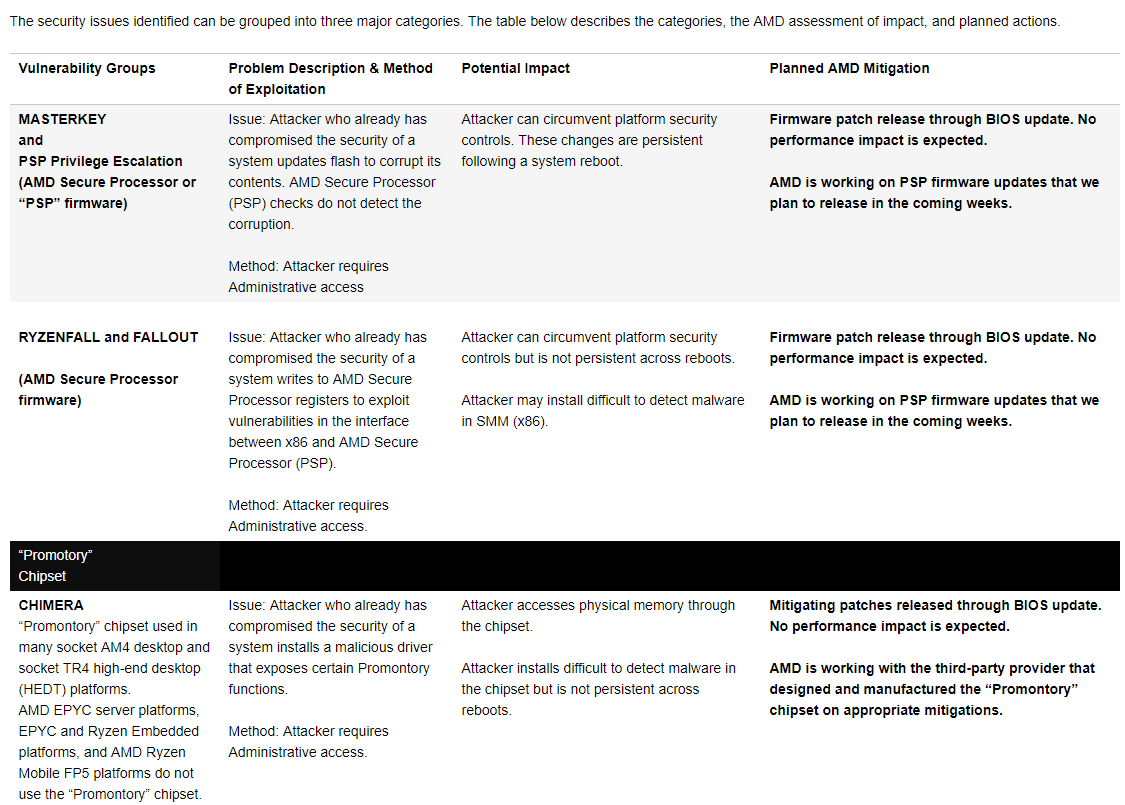
Now, the AMD has come up with a response on the matter. According to a blog post published on Tuesday, the security issues identified by CTS Labs are not related to AMD’s Zen architecture or the exploits disclosed by Google.
“These issues are associated with the firmware managing the embedded security control processor in some of our products (AMD Secure Processor) and the chipset used in some socket AM4 and socket TR4 desktop platforms supporting AMD processors,” the blog post states.
However, AMD also notes that the vulnerabilities can be leveraged only if the attackers have administrative access (or root access) to the system — an opportunity that allows them to do anything from deleting, creating, or modifying files or folders, as well as changing the settings.
But, modern operating systems have built-in security measures to prevent unauthorized administrative access. For instance, Microsoft Windows Credential Guard.
AMD will be releasing firmware patches through BIOS updates in the coming weeks to fix the disclosed vulnerabilities classified as RYZENFALL, FALLOUT, and CHIMERA. The company said there wouldn’t be any effect on the performance.
Also Read: Zuckerberg Facing Heat After Multiple Investigations Into Facebook Data Breach