Beware! This Malicious Ransomware Hides As Free Games & Software

Are you tempted to download free games and software from the internet? If yes, you need to take caution as a new form of ransomware is impersonating itself as free games and software and tricking users to download itself.
Anatova ransomware was first spotted on January 1 by McAfee and has strong encryption using a pair of RSA keys that blocks users from accessing the files stored on their PC. This mechanism is commonly deployed by infamous ransomware families like Crysis and Gandcrab.
The ransomware displays unprecedented tactics to morph itself easily in order to escape popular methods used for detecting ransomware. This indicates that the bad actors behind it are highly experienced malware developers.
Its strong encryption and evasive techniques make it a serious threat to security.
“Anatova has the potential to become very dangerous with its modular architecture which means that new functionalities can easily be added. The malware is written by experienced authors that have embedded enough functionalities to be sure that typical methods to overcome ransomware will be ineffective,” says Christian Beek, a lead scientist and principal engineer working at McAfee.
The ransomware has targeted users in the US, Belgium, the UK, Germany and other countries of the European continent. The United States has the largest number of users affected by it.
After deciding the victim, RSA pair of keys is generated using crypto API. These keys will cipher all strings before generating random keys and initiating the process of ransomware’s complete deployment on the host system.
The ransomware locks the files of your system and to access your files; it is demanding cryptocurrency of 10 Dash which translates to $700.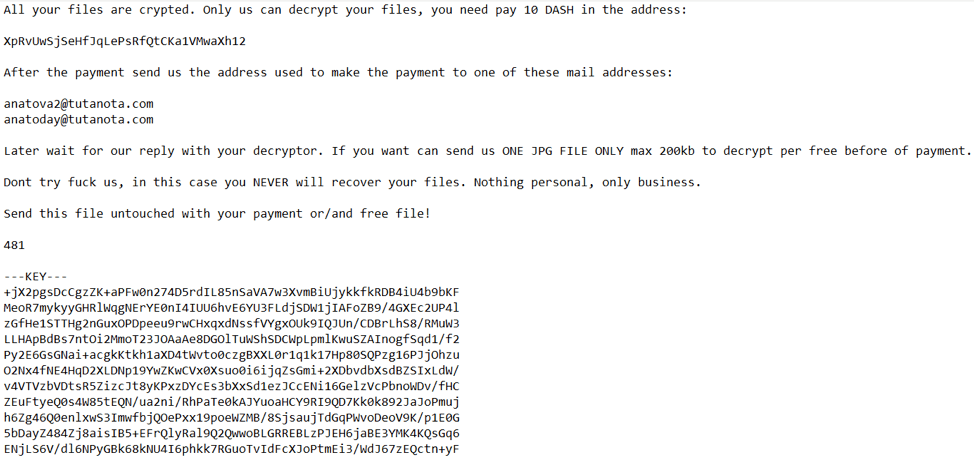 Anatova provides a cryptocurrency wallet address and asks the affected users to email the bad actors behind it to receive the decryption keys. The ransomware displays a message: “Dont try to f*ck us, in this case you NEVER will recover your files. Nothing personal, only business.”
Anatova provides a cryptocurrency wallet address and asks the affected users to email the bad actors behind it to receive the decryption keys. The ransomware displays a message: “Dont try to f*ck us, in this case you NEVER will recover your files. Nothing personal, only business.”
Security researchers are unsure about who is behind the ransomware as of now.
Also Read: China Has Blocked Microsoft’s Bing Search Engine: Report