CAMM2 RAM Standard: Everything You Need To Know About It
RAM is perhaps one of the most crucial aspects of a computer, as it stores all…
The Geek section of Fossbytes features trending developments, features, and useful guides on Linux distros, programming, single board computers, and DIY projects. Here you can also browse new stories on various open source technologies and budding projects.

RAM is perhaps one of the most crucial aspects of a computer, as it stores all…

It’s no secret that Microsoft has fully embraced generative AI, with almost all its products incorporating…

It’s no secret that smartwatches from Indian home-grown brands have witnessed a surge in popularity in…

Solid State Drives (SSDs) have long been a popular choice for people looking to upgrade their…

With Apple transitioning to the M-series of processors, MacBooks have suddenly gained a lot of popularity,…

With the rising costs of smartphones, OnePlus’s strategy has evolved from releasing just one smartphone a…
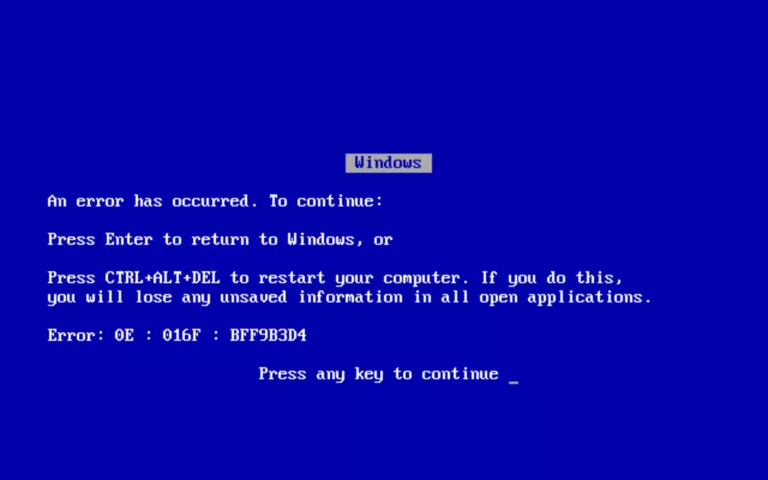
The Blue Screen of Death (BSOD) in Windows has become a bit of a meme over…

Improved apps, AppCenter, and more!
It’s time to switch from Windows 10.
List of Linux Distros For Programming And Development