Leaked NSA Exploits Modified To Attack Every Windows Version Since 2000

Now, Sean Dillion, a security researcher at RiskSense, has modified the source code of three other leaked NSA tools called EnternalRomance, EternalChampion, and EnternalSynergy. In the past, he also ported the EternalBlue exploit to work on Windows 10.
Dillion released the source code on his GitHub repo which includes a disclaimer stating that “the software has been created purely for academic research and for the development of effective defensive techniques.” He won’t use it to attack systems.
The modified exploits are meant to take advantage of the vulnerabilities CVE-2017-0146 and CVE-2017-0143. An attacker can compromise an affected Windows system and perform remote code execution and remote control operations.
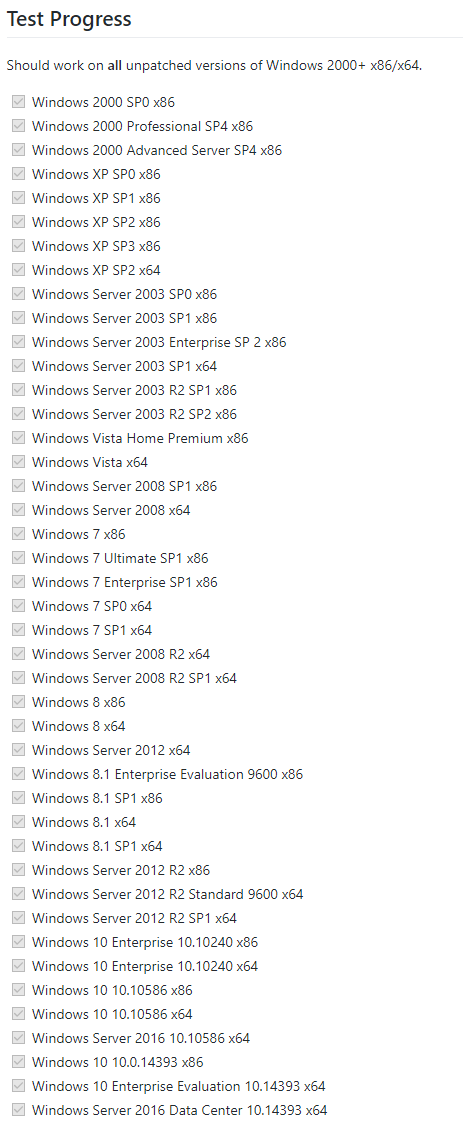
Almost every version of Windows released since Windows 2000 is affected, including the 32-bit and 64-bit variants of Windows Server, Windows XP, Windows 7, Windows Vista, Windows 8, etc.
The list also includes Microsoft’s latest active operating system Windows 10 which is believed to be safe from the modified exploits, provides it’s loaded with all the updates and security fixes. However, the threat remains for older Windows 10 versions that aren’t secured with the patches released in March last year.
What would make it more problematic is the fact that Microsoft has even dropped support for them, for instance, the Anniversary Update (14393) which is among the affected versions.
The exploit module could also bring trouble for corporates which are hesitant when it comes to keeping their software up-to-date, mostly due to compatibility issues.
To know more about the modified NSA exploit module, you can visit Dillion’s repo.
Also Read: 17-Year-Old Boy Arrested For Coding Malware To Steal Cryptocurrency Wallet Passwords