This Hacker is Destroying Racist and Homophobic Websites One by One
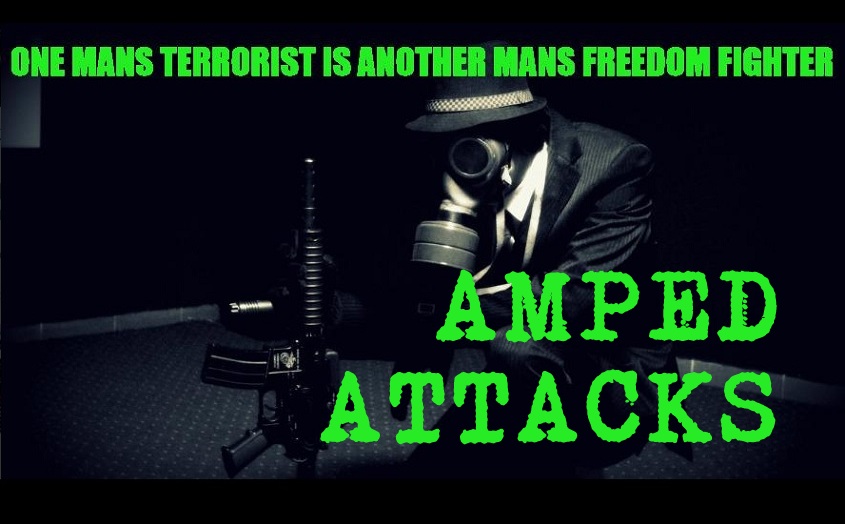
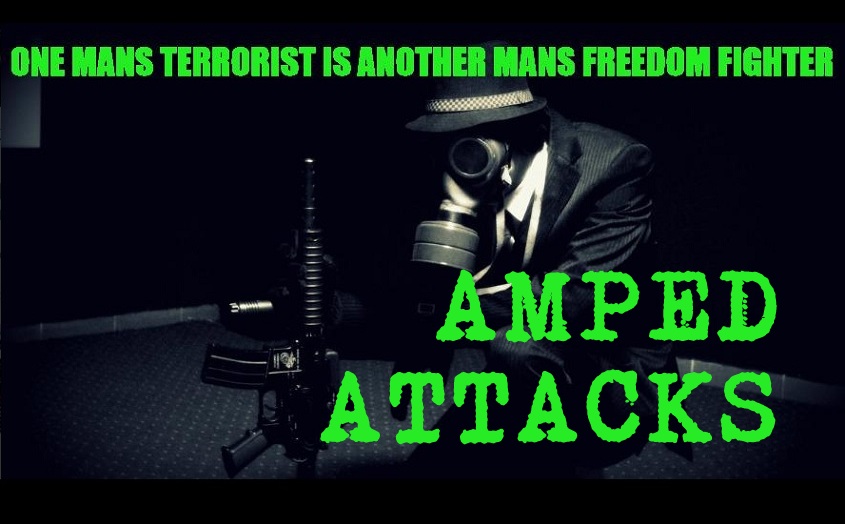 Short Bytes: A hacker that operates a Twitter handle named Amped Attacks, is taking down the websites spreading homophobia and racism one by one. Via the Twitter account, the hacker tweets the next targets and tells the world about its activities.
Short Bytes: A hacker that operates a Twitter handle named Amped Attacks, is taking down the websites spreading homophobia and racism one by one. Via the Twitter account, the hacker tweets the next targets and tells the world about its activities.
The hacker is targeting these websites by deploying the specialized distributed denial-of-service (DDoS) attacks. For those who don’t know, a DDoS attack is a common method of taking down a server and website by flooding it with tons of overloaded requests. As a result, the machine and network resource becomes unavailable and the webpage shows error.
The hacker Amped Attacks uses #tangotown in the tweets, a hashtag that is commonly used by the Anonymous hacktivist group. But, this doesn’t confirm Amped Attacks’ association with the Anonymous.
https://t.co/ZdZp35ACFu #TangoDown pic.twitter.com/jFuqZVxabb
— Amped Attacks (@sgtbilko420) October 22, 2015
None of the official Twitter handlers have mentioned that Amped Attacks is working under their influence. The most recent target of the Amped Attack is website lionmakerstudios.org as shown in the tweet below (website is back online:
https://t.co/CHXsawD1Df @RealLionMaker you asked a 13 year old girl for nudes? enjoy you fucking pedophile pic.twitter.com/rBNIgXBXyO — Amped Attacks (@sgtbilko420) October 23, 2015
Earlier this weekend, the hacker took down kkkknights.com and it even successfully targeted a website related to ISIS. In a recent tweet, the hacker warns another site:
https://t.co/9rHGua2EVN you are my target for tomorrow you have been warned :)
— Amped Attacks (@sgtbilko420) October 21, 2015
It should be noted that these DDoS outages don’t last very long. So, it’s possible that the Amped Attacks is drawing our attention towards these websites and I don’t think that’s a bad thing to do.
i would personally like to thank all of you for the support its nice to see the people against racist and people that cyber bully — Amped Attacks (@sgtbilko420) October 23, 2015
What do you think about these attacks? Tell us in the comments below.