Apple Bug Bounty Now Lets You Earn Up to $1.5 Million

Today, Apple has announced that its bug bounty program is now open to all security researchers. Previously, the bug bounty program was invite-based and not accessible to all security researchers. Now, anyone can disclose a vulnerability in iOS, WatchOS, macOS, tvOS, or iCloud to earn cash rewards under the program.
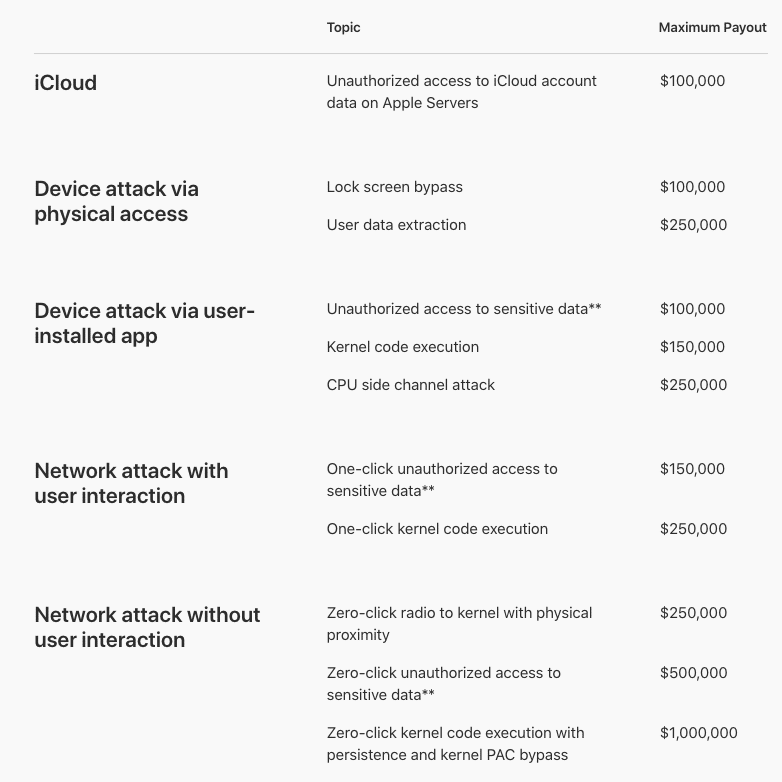
In addition to making its program available for the general public, Apple has also increased the maximum payout from $200,000 to $1 million.
You can earn the maximum bug bounty reward for disclosing a zero-click kernel code execution with persistence and kernel PAC bypass.
On top of that, Apple has also added a 50% bonus to the standard payout if you happen to spot a bug in beta software. This makes it the highest reward in the program, amounting to $1.5 million.
Also, the bonus will be awarded for revealing ‘regressive bugs’ or those bugs that were patched once, but have resurfaced in the latest version of the software. However, it doesn’t apply to all developer betas and public betas.
Here is a list of categories and the maximum payout being offered by Apple under its bug bounty program:
Apple has set the following pre-requisites for availing the cash reward under its program:
- A security researcher must be the first to report the vulnerability to Apple Product Security.
- A working exploit with a clear report must be included.
- The reported vulnerability must not be disclosed to the public before Apple has released the security advisory for the report.
If you manage to fulfill these criteria, you will be eligible to win a cash prize depending upon the complexity and severity of the vulnerability you have reported.
Also Read: How To Get Free Apple Music For 6 Months This Christmas?