Simple Registry Hacks Bypass Windows Digital Signature, Opening Gates For Malicious Code
It’s possible to disable the Windows digital signature check when we face trouble installing drivers. But, it seems that there are other unconventional ways to do it, which could invite unwanted things our computer.
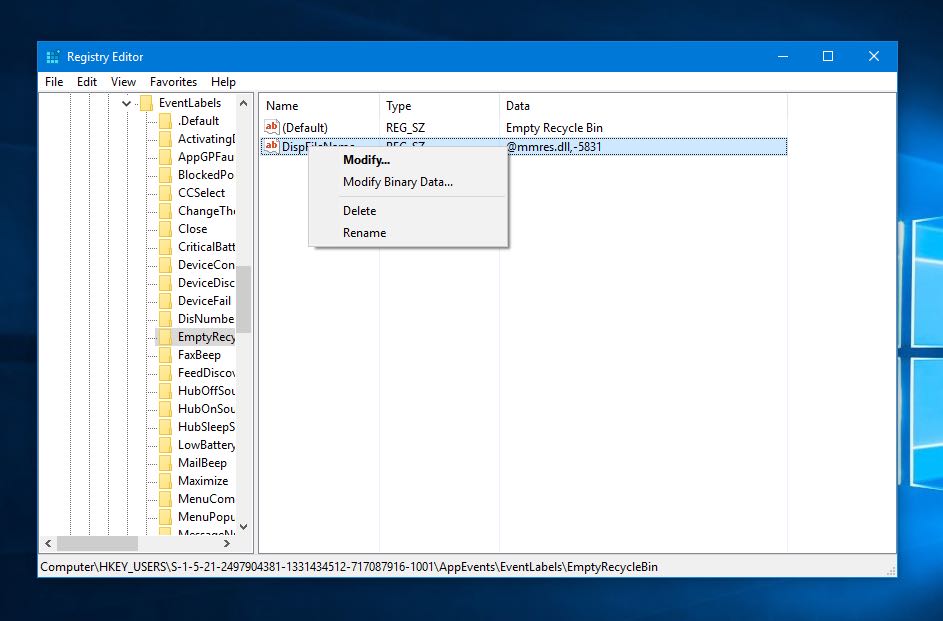
Matt Graeber is a security researcher at SpecterOps, Inc. While speaking at the DerbeyCon 7.0, he talked about the two Windows registry edits he had discovered which can be used to bypass the Windows digital signature check, TechTarget reports. These are also explained in his whitepaper titled “Subverting Trust in Windows“.
Editing one of the two registries would return “the same Microsoft certificate for any executable file whether it has an embedded Authenticode signature or not”, he wrote in the paper.
In the other case, if a file has a legitimate Authenticode certificate embedded (taken from some other valid code), editing the registry would allow the file to dodge the digital signature checking even if the cryptographic keys don’t match.
Matt said that tweaking the registry values doesn’t involve dropping any malicious code onto the system. However, he highlighted the fact that he had admin privileges. But, this doesn’t eliminate the risk of such attacks, as he can gain the privileges remotely.
For the demo, he used a machine which only whitelisted Microsoft signed code; he was able to validate the code “Hello World”, which embedded a Microsoft certificate, by changing registry values.
“I can be whoever I want to be by flipping those two registry values,” he told the audience. “I can be Microsoft or Google or anyone on this compromised system.”
Matt wrote in his paper that code signing and trust validation are critical malware classification components in various antivirus tools. Also, they’re important for application whitelisting tools like Device Guard and App Locker. “Subverting the trust architecture of Windows, in many cases, is also likely to subvert the efficacy of security products.”
When it comes to validating trust, there should be “multiple data entry points” established with the help of different methods, he suggested. We shouldn’t depend on a single signature validation mechanism altogether.
You can read Matt’s paper for more details on this topic. If you have something to add, drop your thoughts in the comments.
Also Read: SafeBrowse Chrome Extension Mines Cryptocurrency Using Your CPU Power