How A Student Fooled 17,000 Coders Into Running His ‘Sketchy’ Programming Code
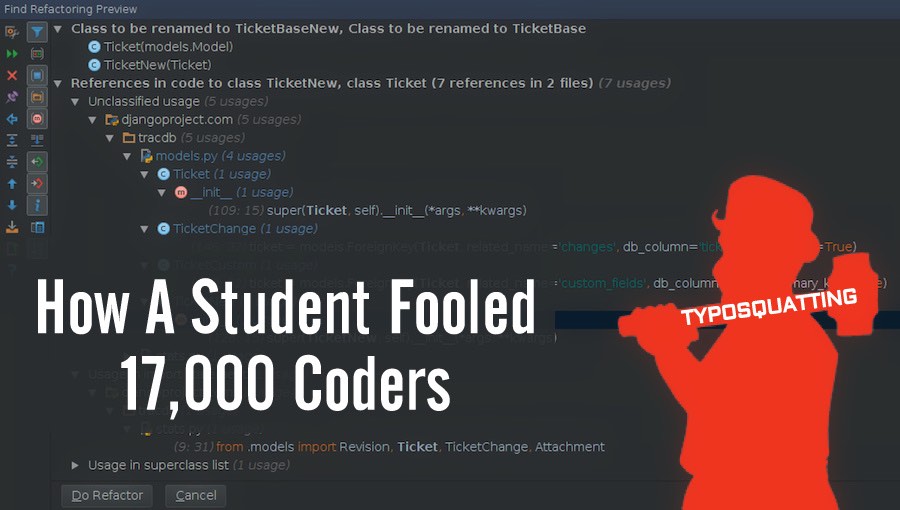
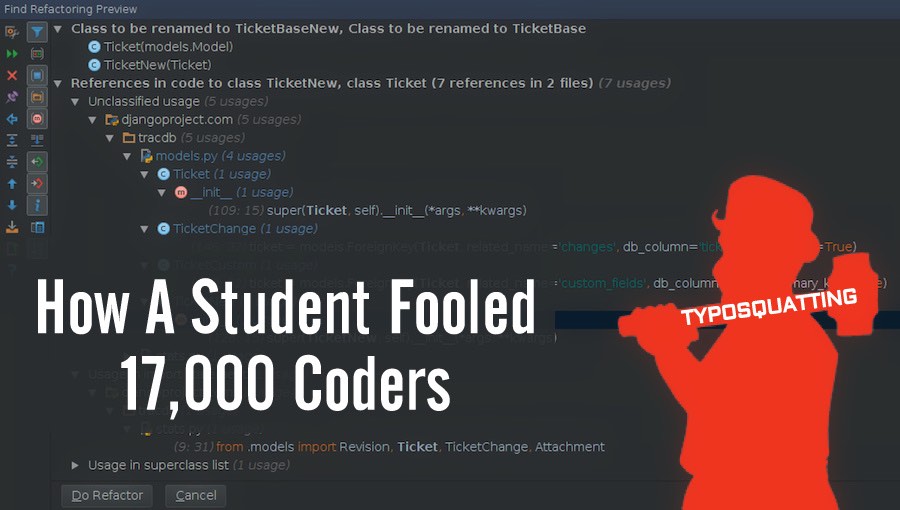 Short Bytes: Using the typosquatting technique, a German college student tricked more than 17,000 people from cybersecurity and programming community into clicking his fake software packages. More than half the time his code ran with administrative rights, affecting government and military organizations.
Short Bytes: Using the typosquatting technique, a German college student tricked more than 17,000 people from cybersecurity and programming community into clicking his fake software packages. More than half the time his code ran with administrative rights, affecting government and military organizations.
The same technique could be used to trick people into installing malicious packages and a person could be fooled into malicious code execution with administrative rights.
A similar technique was used by a German university student who got his code running on the computers of thousands of software developers.
This ethically questionable research was carried out by Nikolai Philipp Tschache, a student of the University of Hamburg, as his bachelor thesis.
Using a variation of typosquatting, he uploaded his code to 3 popular communities of developers–PyPi, RubyGems, NPM–and gave them names of the 214 most downloaded packages on.
As a result, over the span of few months, his sketchy code was executed on more than 17,000 domains and more than 45,000 times. Interestingly, more than half the time his code ran with complete administrative rights. His script was also found to affect .mil domains of the US military.
In his thesis titled “Typosquatting in Programming Language Package Managers”, he writes that he specifically targeted people from cybersecurity and programming community.
Tschache calls it an effort to show the risks posed by typosquatting and develop simple countermeasures to evade these risks.
While the ethicality of this thesis could be a topic of debate, the conclusions deduced are worth reading.
Did you find this article helpful? Don’t forget to drop your feedback in the comments section below.
Pay what you want on this ethical hacker and pentester pro bundle.