How To Enable End-To-End Encryption On Facebook Messenger

With all the commotion that WhatsApp caused with its new privacy policies, people started running toward Signal. However, the detestation for WhatsApp only lasted for a while, and people eventually forgot about Signal. This shows how perplexed people are when it comes to their online privacy.
Being vigilant about your privacy is the need of the hour, and users need to understand that. Although protecting your privacy online gets discussed a lot, the question arises of how do you do it? To keep your chats private and free of invasion, messaging apps provide something called the End To End Encryption(E2E). Let’s talk more about what E2EE means and how to enable it in the popular messaging app called Facebook Messenger.
What is E2EE?

End-to-end encryption (E2EE) is a secure communication method that prevents unauthorized parties from accessing data as it is transferred from one end system or device to another. It is currently one of the most important pillars of online privacy. Some messaging apps that allow E2E are Telegram, Whatsapp, and Signal.
Recently, a Nebraska teenager and her mother were charged with breaking the abortion law. And the medium through which the police came to know about the incident was Facebook chats. However, we do not make any comment on whether the process was correct or not. We want to draw your attention to the importance of online privacy.
There may be several people that may only use Facebook Messenger for texting. And, if someone is persistent in using Facebook Messenger for texting, how do you make it secure? You can start by enabling the E2EE inside the Facebook messenger app on your mobile device( Android or iOS).
How do you enable it?
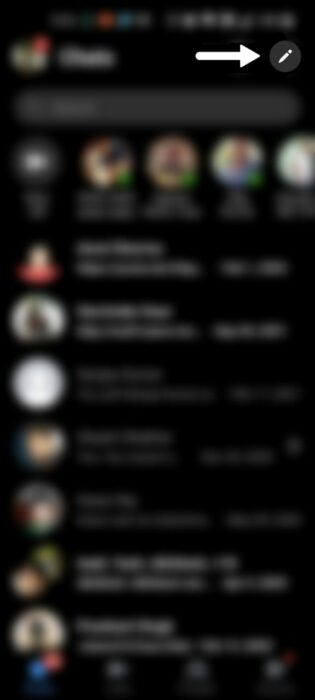
- Go to the bottom menu of the Messenger mobile app and choose Chats.
- In the upper right corner, click the Edit symbol (it looks like a pen).
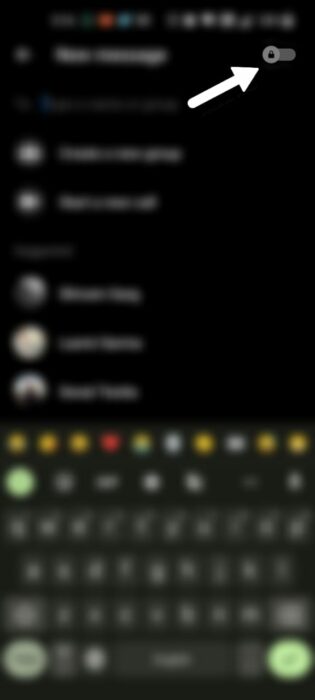
- In the top right corner, toggle the lock icon on.
- And you can start a conversation with the person you choose.
However, you may also enable E2EE if you’re already conversing with the person and decide you want to.
- Tap the information icon on the top right
- Click, Go to secret conversation.
Additionally, you can also activate the Vanish mode.
- Tap the Vanish mode button on the information page.
- Turn on Vanish mode.
Do you have other options?
Although the new privacy policies of Whatsapp do not induce much confidence in the users, it still is the go-to messaging service for many regions. The propensity at which people started recommending Signal died all so quickly.
Besides Whatsapp and Signal, there are also a few other good options. However, you need to do your due diligence and figure out which messaging service suits you best regarding usability and privacy.
Lastly, we’d advise you to be more aware of your online presence and use secure platforms to protect your data. This can also save you from annoying targeted ads. Comment your thoughts on this down below.