Realme P1 5G Review: Best Budget Smartphone of 2024?
Realme has been on a roll in 2024, with new phones launching every month. Keeping up…
Our review section contains in-depth review of new electronic devices and software. We review smartphones, computers, tablets, services, apps, software, etc. Since we’re a small team, of course, we can’t review everything, but we try to keep our review section as cool as possible. You can find affordable wireless headphones, latest smartphones, 3D printers, Linux distros, VPN services, and more.

Realme has been on a roll in 2024, with new phones launching every month. Keeping up…

When Realme first launched the Narzo series in 2020, its primary target was budget-conscious online consumers…

When HP first unveiled the Omen Transcend 14 at CES 2024, it caught the world by…

When you think of vivo, you might imagine a phone focusing on cameras and a premium…

When Lava first re-entered the Indian market, many were skeptical of the brand, considering Chinese smartphones…

It’s no secret that vivo has experienced a resurgence in recent years, thanks in part to…
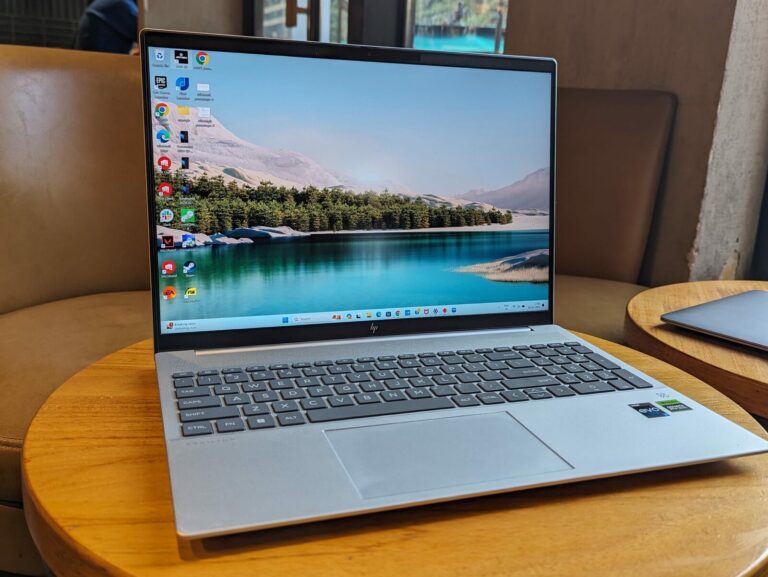
When it comes to productivity laptops, many think of devices with powerful processors that often compromise…

When it comes to the sub-25K INR price segment, we all expect brands to prioritize performance…

When you think of a mid-range or budget phone, you might notice brands prioritizing performance while…

The Ugreen name is becoming synonymous with computer accessories and, in particular, power adapters. I’ve covered…